Mass Surveillance on:
[Wikipedia]
[Google]
[Amazon]
Mass surveillance is the intricate surveillance of an entire or a substantial fraction of a population in order to monitor that group of citizens. The surveillance is often carried out by local and federal governments or
GEOINT Singularity
in which everything on the surface of the earth will be monitored at all times, analyzed by artificial intelligence systems, and then redistributed and made available to the general public globally in realtime.
, Reporters Without Borders, 12 March 2013
HIDE
were funded by the
, AGH - University of Science and Technology (Poland). Retrieved 17 September 2013. develops an intelligent urban environment observation system to register and exchange operational data for the automatic detection, recognition and intelligent processing of all information of
EU Research Projects, Community Research and Development Information Service (CORDIS), European Commission, 4 September 2013. Retrieved 17 September 2013.
Ian Johnston, ''The Telegraph'' (UK), 19 September 2009. Retrieved 17 September 2013. The main expected results of the INDECT project are: * Trial of intelligent analysis of video and audio data for threat detection in urban environments, * Creation of tools and technology for privacy and data protection during storage and transmission of information using quantum cryptography and new methods of digital watermarking, * Performing computer-aided detection of threats and targeted crimes in Internet resources with privacy-protecting solutions, * Construction of a search engine for rapid semantic search based on watermarking of content related to child pornography and human organ trafficking, * Implementation of a distributed computer system that is capable of effective intelligent processing. HIDE ("Homeland Security, Biometric Identification & Personal Detection Ethics") was a research project funded by the European Commission within the scope of the Seventh RTD Framework Programme (FP7). The consortium, coordinated by Emilio Mordini, explored the
Digital Civil Rights in Europe, EDRI-gram Number 2.14, 15 July 2004. Retrieved 17 September 2013. The Dutch military intelligence service MIVD operates a satellite ground station to intercept foreign satellite links and also a facility to eavesdrop on foreign high-frequency radio traffic. An example of mass surveillance carried out by corporations in the Netherlands is an initiative started by five Dutch banks (ABN AMRO, ING, Rabobank, Triodos Bank and de Volksbank). In July 2020 these five banks have decided to establish Transaction Monitoring Netherlands (TMNL) in the collective fight against money laundering and the financing of terrorism. The goal of TMNL-organization is to gather all transaction information provided by Dutch banks in a centralized database to enable full-scale collective transaction monitoring. Preparations have been started but the actual monitoring by TMNL can start after an amendment of the Dutch Anti-Money Laundering and Anti-Terrorist Financing Act.
''Constitution of Russia''. Retrieved 17 September 2013.
"Advanced Scientific - Research Projects"
enterprise St. Petersburg. Within the framework of the practical use of the system of the Ministry of Internal Affairs of the Russian Federation, it has made it possible to identify and solve grave and especially grave crimes, the system is also operated by other state services and departments;
 The
The
2000 Chapter 23, UK Government Legislation. Retrieved 28 September 2013. In 2002 the UK government announced plans to extend the Regulation of Investigatory Powers Act so that at least 28 government departments would be given powers to access
Home Office, 11 February 2011. Retrieved 28 September 2013. Supported by all three major political parties, the UK Parliament passed the
, Associated Press (AP), 2 August 2013. Created in 2001 following the anthrax attacks that killed five people, it is a sweeping expansion of a 100-year-old program called "
Ron Nixon, ''The New York Times'', 3 July 2013. Retrieved 25 September 2013. The FBI developed the computer programs "
 Examples of early surveillance states include the former
Examples of early surveillance states include the former
 An electronic
An electronic
''The Electronic Police State: 2008 National Rankings''
, by Jonathan Logan, Cryptohippie USA. Electronic police states also engage in mass government surveillance of
"Applications of Social Control Theory: Criminality and Governmentality"
, ''International Journal of Asian Social Science'', Vol. 2, No. 7, pp.1026-1032. Seventeen factors for judging the development of an electronic police state were suggested in ''The Electronic Police State: 2008 National Rankings'': * Daily documents: Requirement for the use and tracking of state-issued identity documents and registration. * Border and travel control: Inspections at borders, searching computers and cell phones, demanding decryption of data, and tracking travel within as well as to and from a country. * Financial tracking: A state's ability to record and search financial transactions: checks, credit cards, wires, etc. * Gag orders: Restrictions on and criminal penalties for the disclosure of the existence of state surveillance programs. * Anti-crypto laws: Outlawing or restricting
 The concept of being monitored by our governments collects a large audience of curious citizens. Mass surveillance has been prominently featured in a wide array of books, films, and other media. Advances in technology over the last century have led to possible social control through the Internet and the conditions of late capitalism. Many directors and writers have been enthralled with the potential stories that could come from mass surveillance. Perhaps the most iconic example of fictional mass surveillance is George Orwell's 1949 novel ''
The concept of being monitored by our governments collects a large audience of curious citizens. Mass surveillance has been prominently featured in a wide array of books, films, and other media. Advances in technology over the last century have led to possible social control through the Internet and the conditions of late capitalism. Many directors and writers have been enthralled with the potential stories that could come from mass surveillance. Perhaps the most iconic example of fictional mass surveillance is George Orwell's 1949 novel ''
"The State and Surveillance: Fear and Control"
Didier Bigo and Mireille Delmas-Marty, ''La Clé des Langues'', 23 September 2011,. {{DEFAULTSORT:Mass Surveillance * Human rights Security National security Law enforcement Law enforcement techniques Crime prevention Counterterrorism
governmental organizations
A government or state agency, sometimes an appointed commission, is a permanent or semi-permanent organization in the machinery of government that is responsible for the oversight and administration of specific functions, such as an administratio ...
, such as organizations like the NSA
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
, but it may also be carried out by corporations (either on behalf of governments or at their own initiative). Depending on each nation's laws and judicial systems, the legality of and the permission required to engage in mass surveillance varies. It is the single most indicative distinguishing trait of totalitarian regimes
Totalitarianism is a form of government and a political system that prohibits all opposition parties, outlaws individual and group opposition to the state and its claims, and exercises an extremely high if not complete degree of control and reg ...
. It is also often distinguished from targeted surveillance
Targeted surveillance (or targeted interception) is a form of surveillance, such as wiretapping, that is directed towards specific persons of interest, and is distinguishable from mass surveillance (or bulk interception). Both untargeted and targ ...
.
Mass surveillance has often been cited as necessary to fight terrorism
Terrorism, in its broadest sense, is the use of criminal violence to provoke a state of terror or fear, mostly with the intention to achieve political or religious aims. The term is used in this regard primarily to refer to intentional violen ...
, prevent crime
In ordinary language, a crime is an unlawful act punishable by a State (polity), state or other authority. The term ''crime'' does not, in modern criminal law, have any simple and universally accepted definition,Farmer, Lindsay: "Crime, definit ...
and social unrest
Civil disorder, also known as civil disturbance, civil unrest, or social unrest is a situation arising from a mass act of civil disobedience (such as a demonstration, riot, strike, or unlawful assembly) in which law enforcement has difficulty ...
, protect national security
National security, or national defence, is the security and defence of a sovereign state, including its citizens, economy, and institutions, which is regarded as a duty of government. Originally conceived as protection against military atta ...
, and control the population. At the same time, mass surveillance has equally often been criticized for violating privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
rights, limiting civil and political rights and freedoms, and being illegal under some legal or constitutional systems. Another criticism is that increasing mass surveillance could lead to the development of a surveillance state or an electronic police state
Mass surveillance is the intricate surveillance of an entire or a substantial fraction of a population in order to monitor that group of citizens. The surveillance is often carried out by local and federal governments or governmental organizati ...
where civil liberties are infringed or political dissent is undermined by COINTELPRO
COINTELPRO (syllabic abbreviation derived from Counterintelligence, Counter Intelligence Program; 1956–1971) was a series of Covert operation, covert and illegal projects actively conducted by the United States Federal Bureau of Investigation ( ...
-like programs. Such a state could be referred to as a totalitarian state
Totalitarianism is a form of government and a political system that prohibits all opposition parties, outlaws individual and group opposition to the state and its claims, and exercises an extremely high if not complete degree of control and regul ...
.
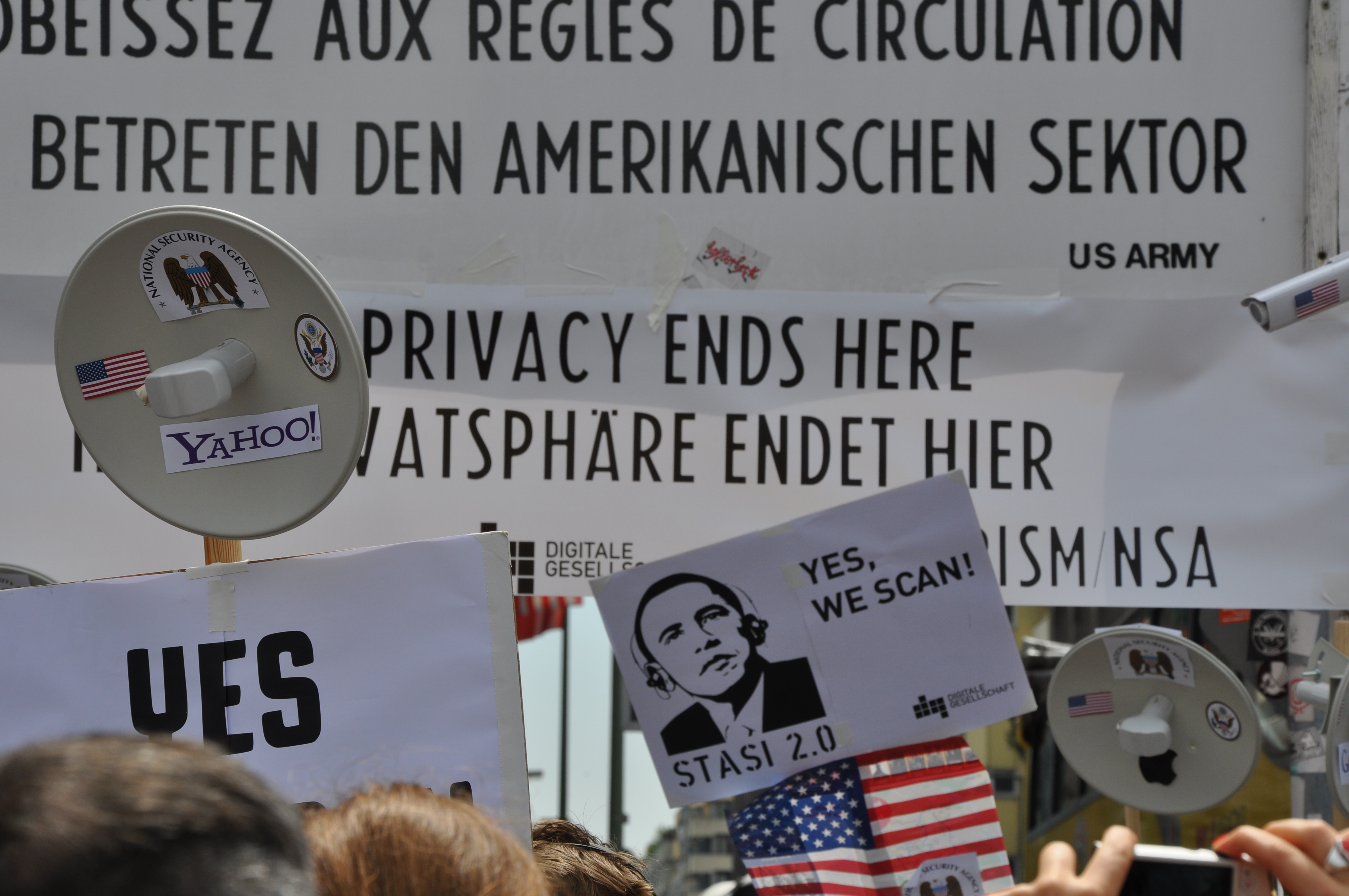
In 2013, the practice of mass surveillance by world governments was called into question after Edward Snowden
Edward Joseph Snowden (born June 21, 1983) is an American and naturalized Russian former computer intelligence consultant who leaked highly classified information from the National Security Agency (NSA) in 2013, when he was an employee and su ...
's 2013 global surveillance disclosure on the practices by the National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
(NSA) of the United States. Reporting based on documents Snowden leaked to various media outlets triggered a debate about civil liberties and the right to privacy
The right to privacy is an element of various legal traditions that intends to restrain governmental and private actions that threaten the privacy of individuals. Over 150 national constitutions mention the right to privacy. On 10 December 194 ...
in the Digital Age
The Information Age (also known as the Computer Age, Digital Age, Silicon Age, or New Media Age) is a historical period that began in the mid-20th century. It is characterized by a rapid shift from traditional industries, as established during t ...
. Mass surveillance is considered a global issue. The Aerospace Corporation
The Aerospace Corporation is an American nonprofit corporation that operates a federally funded research and development center (FFRDC) in El Segundo, California. The corporation provides technical guidance and advice on all aspects of space mi ...
of the United States describes a near-future event they call theGEOINT Singularity
in which everything on the surface of the earth will be monitored at all times, analyzed by artificial intelligence systems, and then redistributed and made available to the general public globally in realtime.
By country
Privacy International
Privacy International (PI) is a UK-based registered charity that defends and promotes the right to privacy across the world. First formed in 1990, registered as a non-profit company in 2002 and as a charity in 2012, PI is based in London. Its c ...
's 2007 survey, covering 47 countries, indicated that there had been an increase in surveillance and a decline in the performance of privacy safeguards, compared to the previous year. Balancing these factors, eight countries were rated as being 'endemic surveillance societies'. Of these eight, China
China, officially the People's Republic of China (PRC), is a country in East Asia. It is the world's most populous country, with a population exceeding 1.4 billion, slightly ahead of India. China spans the equivalent of five time zones and ...
, Malaysia
Malaysia ( ; ) is a country in Southeast Asia. The federation, federal constitutional monarchy consists of States and federal territories of Malaysia, thirteen states and three federal territories, separated by the South China Sea into two r ...
and Russia
Russia (, , ), or the Russian Federation, is a List of transcontinental countries, transcontinental country spanning Eastern Europe and North Asia, Northern Asia. It is the List of countries and dependencies by area, largest country in the ...
scored lowest, followed jointly by Singapore
Singapore (), officially the Republic of Singapore, is a sovereign island country and city-state in maritime Southeast Asia. It lies about one degree of latitude () north of the equator, off the southern tip of the Malay Peninsula, borde ...
and the United Kingdom
The United Kingdom of Great Britain and Northern Ireland, commonly known as the United Kingdom (UK) or Britain, is a country in Europe, off the north-western coast of the continental mainland. It comprises England, Scotland, Wales and North ...
, then jointly by Taiwan
Taiwan, officially the Republic of China (ROC), is a country in East Asia, at the junction of the East and South China Seas in the northwestern Pacific Ocean, with the People's Republic of China (PRC) to the northwest, Japan to the nort ...
, Thailand
Thailand ( ), historically known as Siam () and officially the Kingdom of Thailand, is a country in Southeast Asia, located at the centre of the Indochinese Peninsula, spanning , with a population of almost 70 million. The country is bo ...
and the United States
The United States of America (U.S.A. or USA), commonly known as the United States (U.S. or US) or America, is a country primarily located in North America. It consists of 50 states, a federal district, five major unincorporated territorie ...
. The best ranking was given to Greece
Greece,, or , romanized: ', officially the Hellenic Republic, is a country in Southeast Europe. It is situated on the southern tip of the Balkans, and is located at the crossroads of Europe, Asia, and Africa. Greece shares land borders with ...
, which was judged to have 'adequate safeguards against abuse'.
Many countries throughout the world have already been adding thousands of surveillance cameras
Closed-circuit television (CCTV), also known as video surveillance, is the use of video cameras to transmit a signal to a specific place, on a limited set of monitors. It differs from broadcast television in that the signal is not openly tr ...
to their urban, suburban and even rural areas. For example, in September 2007 the American Civil Liberties Union
The American Civil Liberties Union (ACLU) is a nonprofit organization founded in 1920 "to defend and preserve the individual rights and liberties guaranteed to every person in this country by the Constitution and laws of the United States". T ...
(ACLU) stated that we are "in danger of tipping into a genuine surveillance society completely alien to American values" with "the potential for a dark future where our every move, our every transaction, our every communication is recorded, compiled, and stored away, ready to be examined and used against us by the authorities whenever they want".
On 12 March 2013, Reporters Without Borders published a ''Special report on Internet Surveillance''. The report included a list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and human rights. Five countries were placed on the initial list: Bahrain
Bahrain ( ; ; ar, البحرين, al-Bahrayn, locally ), officially the Kingdom of Bahrain, ' is an island country in Western Asia. It is situated on the Persian Gulf, and comprises a small archipelago made up of 50 natural islands and an ...
, China
China, officially the People's Republic of China (PRC), is a country in East Asia. It is the world's most populous country, with a population exceeding 1.4 billion, slightly ahead of India. China spans the equivalent of five time zones and ...
, Iran
Iran, officially the Islamic Republic of Iran, and also called Persia, is a country located in Western Asia. It is bordered by Iraq and Turkey to the west, by Azerbaijan and Armenia to the northwest, by the Caspian Sea and Turkmeni ...
, Syria
Syria ( ar, سُورِيَا or سُورِيَة, translit=Sūriyā), officially the Syrian Arab Republic ( ar, الجمهورية العربية السورية, al-Jumhūrīyah al-ʻArabīyah as-Sūrīyah), is a Western Asian country loc ...
, and Vietnam
Vietnam or Viet Nam ( vi, Việt Nam, ), officially the Socialist Republic of Vietnam,., group="n" is a country in Southeast Asia, at the eastern edge of mainland Southeast Asia, with an area of and population of 96 million, making i ...
.''The Enemies of the Internet Special Edition : Surveillance'', Reporters Without Borders, 12 March 2013
Australia
Bahrain
Bahrain
Bahrain ( ; ; ar, البحرين, al-Bahrayn, locally ), officially the Kingdom of Bahrain, ' is an island country in Western Asia. It is situated on the Persian Gulf, and comprises a small archipelago made up of 50 natural islands and an ...
is one of the five countries on Reporters Without Borders' March 2013 list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and human rights. The level of Internet filtering and surveillance in Bahrain is one of the highest in the world. The royal family is represented in all areas of Internet management and has sophisticated tools at its disposal for spying on its subjects. The online activities of dissidents and news providers are closely monitored and the surveillance is increasing.
Media reports published in July 2021 exposed the use of NSO Group
NSO Group Technologies (NSO standing for Niv, Shalev and Omri, the names of the company's founders) is an Israeli cyber-intelligence firm primarily known for its proprietary spyware Pegasus, which is capable of remote zero-click surveillance ...
's phone malware software, Pegasus, for spying on rights activists, lawyers, and journalists, globally, by authoritarian governments. Bahrain was among the many countries listed as the Israeli firm's clients accused of hacking and conducting unauthorized mass surveillance using phone malware despite a poor human rights record. The software is said to infect devices, allowing its operators to get access to the target's messages, photos, record calls, and activate the microphone and camera.
Yusuf al-Jamri had no idea that even after fleeing Bahrain, he won’t be able to escape the government’s prying eyes, even after taking asylum in the UK. After moving to the UK and getting his asylum request accepted, Al-Jamri legally filed charges against Bahrain along with the notorious spyware firm, NSO Group for infecting his phone with a malware, built with military-grade technology in August 2019. The hacking was verified by the researchers at Toronto based CitizenLab. As a result of which Yusuf complained of being subjected to personal injury, loss of privacy, distress and anxiety. Al-Jamri’s lawyers made claims about the same in a pre-claim letter sent to both the accused, NSO Group and the Bahraini government. No response was received from the two on being approached for comments.
Canada
China
China
China, officially the People's Republic of China (PRC), is a country in East Asia. It is the world's most populous country, with a population exceeding 1.4 billion, slightly ahead of India. China spans the equivalent of five time zones and ...
is one of the five countries on Reporters Without Borders' March 2013 list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and basic human rights. All Internet access in China is owned or controlled by the state or the Chinese Communist Party
The Chinese Communist Party (CCP), officially the Communist Party of China (CPC), is the founding and One-party state, sole ruling party of the China, People's Republic of China (PRC). Under the leadership of Mao Zedong, the CCP emerged victoriou ...
. Many foreign journalists in China have said that they take for granted that their telephones are tapped and their email is monitored.
The tools put in place to filter and monitor the Internet are collectively known as the Great Firewall of China
The Great Firewall (''GFW''; ) is the combination of legislative actions and technologies enforced by the People's Republic of China to regulate the Internet domestically. Its role in internet censorship in China is to block access to selected for ...
. Besides the usual routing regulations that allow access to an IP address or a particular domain name to be blocked, the Great Firewall makes large-scale use of Deep Packet Inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is oft ...
(DPI) technology to monitor and block access based on keyword detection. The Great Firewall has the ability to dynamically block encrypted
In cryptography, encryption is the process of encoding information. This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext. Ideally, only authorized parties can deci ...
connections. One of the country's main ISPs, China Unicom
China United Network Communications Group Co., Ltd. () or China Unicom () (CUniq in short) is a Chinese state-owned telecommunications operator. Started as a wireless paging and GSM mobile operator, it currently provides a range of services i ...
, automatically cuts a connection as soon as it is used to transmit encrypted content.
The monitoring system developed by China is not confined to the Great Firewall, monitoring is also built into social networks, chat services and VoIP. Private companies are directly responsible to the Chinese authorities for surveillance of their networks to ensure banned messages are not circulated. The QQ application, owned by the firm Tencent, allows the authorities to monitor in detail exchanges between Internet users by seeking certain keywords and expressions. The author of each message can be identified by his or her user number. The QQ application is effectively a giant Trojan horse. And since March 2012, new legislation requires all new users of micro-blogging sites to register using their own name and telephone number.
Skype
Skype () is a proprietary telecommunications application operated by Skype Technologies, a division of Microsoft, best known for VoIP-based videotelephony, videoconferencing and voice calls. It also has instant messaging, file transfer, deb ...
, one of the world's most popular Internet telephone platforms, is closely monitored. Skype services in China are available through a local partner, the TOM media group. The Chinese-language version of Skype, known as TOM-Skype
TOM Group Limited () is a Chinese-language media company in the Greater China region, with business interests across markets in Mainland China, Taiwan and Hong Kong. Its business covers four media sectors, Internet ( TOM Online), Outdoor (TOM Ou ...
, is slightly different from the downloadable versions in other countries. A report by OpenNet Initiative Asia says everyday conversations are captured on servers. Interception and storage of a conversation may be triggered by a sender's or recipient's name or by keywords that occur in the conversation.
On 31 January 2013, ''The New York Times
''The New York Times'' (''the Times'', ''NYT'', or the Gray Lady) is a daily newspaper based in New York City with a worldwide readership reported in 2020 to comprise a declining 840,000 paid print subscribers, and a growing 6 million paid ...
'' reported that it had been the target of attacks by the Chinese hackers. The first breach took place on 13 September 2012 when the newspaper was preparing to publish an article about the fortune amassed by the family of outgoing Prime Minister Wen Jiabao
Wen Jiabao (born 15 September 1942) is a retired Chinese politician who served as the Premier of the State Council from 2003 to 2013. In his capacity as head of government, Wen was regarded as the leading figure behind China's economic policy ...
. The newspaper said the purpose of attacks was to identify the sources that supplied the newspaper with information about corruption among the prime minister's entourage. ''The Wall Street Journal
''The Wall Street Journal'' is an American business-focused, international daily newspaper based in New York City, with international editions also available in Chinese and Japanese. The ''Journal'', along with its Asian editions, is published ...
'' and ''CNN
CNN (Cable News Network) is a multinational cable news channel headquartered in Atlanta, Georgia, U.S. Founded in 1980 by American media proprietor Ted Turner and Reese Schonfeld as a 24-hour cable news channel, and presently owned by ...
'' also said they had been the targets of cyber attacks from China. In February, Twitter
Twitter is an online social media and social networking service owned and operated by American company Twitter, Inc., on which users post and interact with 280-character-long messages known as "tweets". Registered users can post, like, and ...
disclosed that the accounts of some 250,000 subscribers had been the victims of attacks from China similar to those carried out on ''The New York Times''. Mandiant, the company engaged by the NYT to secure its network, identified the source of the attacks as a group of hackers it called Advanced Persistent Threat 1, a unit of the People's Liberation Army operating from a 12-story building in the suburbs of Shanghai that had hundreds, possibly thousands, of staff and the direct support of the Chinese government.
The newest form of mass surveillance in China is the Social Credit System
The Social Credit System () is a national credit rating and blacklist being developed by the government of the People's Republic of China. The social credit initiative calls for the establishment of a record system so that businesses, indivi ...
, where citizens and businesses are given or deducted good points based on social behavior such as adherence to laws, honesty, tax evasion or political activism. Individuals can also be subject to travel restrictions such as bans on purchases of flights and high speed train tickets based on whether they have violated social norms, certain laws or engage in political activism against the government, subjecting violators to a form of virtual house arrest by confining them to a specific geographic area such as a particular town or city. The Chinese government also plans to network and interlink up to 20 million surveillance cameras equipped with facial recognition as part of the 'Skynet' project in order to track down wanted fugitives and suspects within minutes.
According to UK-based technology research organization, Comparitech, a city in China
China, officially the People's Republic of China (PRC), is a country in East Asia. It is the world's most populous country, with a population exceeding 1.4 billion, slightly ahead of India. China spans the equivalent of five time zones and ...
called Chongqing is the most surveilled city in the entire world, with 2.5m cameras watching over almost 15.35 million people. As per the data accumulated, the Chinese city beats Shanghai
Shanghai (; , , Standard Mandarin pronunciation: ) is one of the four direct-administered municipalities of the People's Republic of China (PRC). The city is located on the southern estuary of the Yangtze River, with the Huangpu River flow ...
, Beijing
}
Beijing ( ; ; ), alternatively romanized as Peking ( ), is the capital of the People's Republic of China. It is the center of power and development of the country. Beijing is the world's most populous national capital city, with over 21 ...
, and Shenzhen
Shenzhen (; ; ; ), also historically known as Sham Chun, is a major sub-provincial city and one of the special economic zones of China. The city is located on the east bank of the Pearl River estuary on the central coast of southern province ...
, in terms of mass surveillance in China
Mass surveillance in the People's Republic of China (PRC) is the network of monitoring systems used by the Chinese central government to monitor Chinese citizens. It is primarily conducted through the government, although corporate surveillance ...
.
Internet surveillance is pervasive within China, under the Cybersecurity Law of the People's Republic of China
The Cybersecurity Law of the People's Republic of China, ( Chinese: 中华人民共和国网络安全法) commonly referred to as the Chinese Cybersecurity Law, was enacted by the National People’s Congress with the aim of increasing data prote ...
, all SIM cards purchases require real name registration, all WiFi hotspots throughout the country require SMS verification through a phone number which is incidentally linked to a user's resident ID card and all instant messaging and internet service providers including but not limited to ISP's, internet cafes and gaming service providers are required to verify the real identity of users through either a foreign passport or national ID card prior to the provision of a service. All domestic flight tickets and purchases of high speed train tickets and banking and financial services also require real name ID in order to be provided in order to be purchased.
East Germany
Before the Digital Revolution, one of the world's biggest mass surveillance operations was carried out by the Stasi, thesecret police
Secret police (or political police) are intelligence, security or police agencies that engage in covert operations against a government's political, religious, or social opponents and dissidents. Secret police organizations are characteristic of ...
of the former East Germany
East Germany, officially the German Democratic Republic (GDR; german: Deutsche Demokratische Republik, , DDR, ), was a country that existed from its creation on 7 October 1949 until its dissolution on 3 October 1990. In these years the state ...
. By the time the state collapsed in 1989, the Stasi had built up an estimated civilian network of 189,000 informants, who monitored even minute hints of political dissent among other citizens. Many West Germans visiting friends and family in East Germany were also subject to Stasi spying, as well as many high-ranking West German politicians and persons in the public eye.
Most East German citizens were well aware that their government was spying on them, which led to a culture of mistrust: touchy political issues were only discussed in the comfort of their own four walls and only with the closest of friends and family members, while widely maintaining a façade of unquestioning followership in public.
European Union
The right toprivacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
is a highly developed area of law in Europe. The Data Protection Directive
The Data Protection Directive, officially Directive 95/46/EC, enacted in October 1995, is a European Union directive which regulates the processing of personal data within the European Union (EU) and the free movement of such data. The Data Pro ...
regulates the processing of personal data within the European Union
The European Union (EU) is a supranational political and economic union of member states that are located primarily in Europe. The union has a total area of and an estimated total population of about 447million. The EU has often been des ...
. For comparison, the US has no data protection law that is comparable to this; instead, the US regulates data protection on a sectoral basis.
Since early 2012, the European Union has been working on a General Data Protection Regulation to replace the Data Protection Directive and harmonise data protection and privacy law. On 20 October 2013, a committee at the European Parliament
The European Parliament (EP) is one of the legislative bodies of the European Union and one of its seven institutions. Together with the Council of the European Union (known as the Council and informally as the Council of Ministers), it adopts ...
backed the measure, which, if it is enacted, could require American companies to seek clearance from European officials before complying with United States warrants seeking private data. The vote is part of efforts in Europe to shield citizens from online surveillance in the wake of revelations about a far-reaching spying program by the U.S. National Security Agency. European Union justice and rights commissioner Viviane Reding said "The question has arisen whether the large-scale collection and processing of personal information under US surveillance programmes is necessary and proportionate to meet the interests of national security." The EU is also asking the US for changes to US legislation to match the legal redress offered in Europe; American citizens in Europe can go to the courts if they feel their rights are infringed but Europeans without right of residence in America cannot. When the EU / US arrangement to implement International Safe Harbor Privacy Principles
The International Safe Harbor Privacy Principles or Safe Harbour Privacy Principles were principles developed between 1998 and 2000 in order to prevent private organizations within the European Union or United States which store customer data from ...
were struck down by the European Court of Justice, a new framework for transatlantic data flows, called the " EU-US Privacy Shield", was adopted in July 2016.
In April 2014, the European Court of Justice declared invalid the EU Data Retention Directive. The Court said it violates two basic rights – respect for private life and protection of personal data. The legislative body of the European Union
The European Union (EU) is a supranational political and economic union of member states that are located primarily in Europe. The union has a total area of and an estimated total population of about 447million. The EU has often been des ...
passed the Data Retention Directive on 15 December 2005. It requires that telecommunication operators retain metadata for telephone, Internet, and other telecommunication services for periods of not less than six months and not more than two years from the date of the communication as determined by each EU member state and, upon request, to make the data available to various governmental bodies. Access to this information is not limited to investigation of serious crimes, nor is a warrant required for access.
Undertaken under the ''Seventh Framework Programme
The Framework Programmes for Research and Technological Development, also called Framework Programmes or abbreviated FP1 to FP9, are funding programmes created by the European Union/European Commission to support and foster research in the Europe ...
'' ''for research and technological development'' (FP7 - Science in Society) some multidisciplinary and mission oriented mass surveillance activities (for example INDECT
INDECT is a research project in the area of intelligent security systems performed by several European universities since 2009 and funded by the European Union. The purpose of the project is to involve European scientists and researchers in the d ...
anHIDE
were funded by the
European Commission
The European Commission (EC) is the executive of the European Union (EU). It operates as a cabinet government, with 27 members of the Commission (informally known as "Commissioners") headed by a President. It includes an administrative body o ...
in association with industrial partners.
The INDECT Project ("Intelligent information system supporting observation, searching and detection for security of citizens in urban environment")INDECT project homepage, AGH - University of Science and Technology (Poland). Retrieved 17 September 2013. develops an intelligent urban environment observation system to register and exchange operational data for the automatic detection, recognition and intelligent processing of all information of
abnormal behaviour
Abnormality (or dysfunctional behavior) is a behavioral characteristic assigned to those with conditions that are regarded as rare or dysfunctional. Behavior is considered to be abnormal when it is atypical or out of the ordinary, consists of un ...
or violence."INDECT: Intelligent information system supporting observation, searching and detection for security of citizens in urban environment"EU Research Projects, Community Research and Development Information Service (CORDIS), European Commission, 4 September 2013. Retrieved 17 September 2013.
Ian Johnston, ''The Telegraph'' (UK), 19 September 2009. Retrieved 17 September 2013. The main expected results of the INDECT project are: * Trial of intelligent analysis of video and audio data for threat detection in urban environments, * Creation of tools and technology for privacy and data protection during storage and transmission of information using quantum cryptography and new methods of digital watermarking, * Performing computer-aided detection of threats and targeted crimes in Internet resources with privacy-protecting solutions, * Construction of a search engine for rapid semantic search based on watermarking of content related to child pornography and human organ trafficking, * Implementation of a distributed computer system that is capable of effective intelligent processing. HIDE ("Homeland Security, Biometric Identification & Personal Detection Ethics") was a research project funded by the European Commission within the scope of the Seventh RTD Framework Programme (FP7). The consortium, coordinated by Emilio Mordini, explored the
ethical
Ethics or moral philosophy is a branch of philosophy that "involves systematizing, defending, and recommending concepts of right and wrong behavior".''Internet Encyclopedia of Philosophy'' The field of ethics, along with aesthetics, concerns ma ...
and privacy
Privacy (, ) is the ability of an individual or group to seclude themselves or information about themselves, and thereby express themselves selectively.
The domain of privacy partially overlaps with security, which can include the concepts of a ...
implications of biometrics
Biometrics are body measurements and calculations related to human characteristics. Biometric authentication (or realistic authentication) is used in computer science as a form of identification and access control. It is also used to identify i ...
and personal detection technologies, focusing on the continuum between personal detection, authentication, identification and mass surveillance.
France
Germany
In 2002 German citizens were tipped off about wiretapping when a software error led to a phone number allocated to theGerman Secret Service
The Federal Intelligence Service (German: ; , BND) is the foreign intelligence agency of Germany, directly subordinate to the Chancellor's Office. The BND headquarters is located in central Berlin and is the world's largest intelligence head ...
being listed on mobile telephone bills.
India
The Indian parliament passed theInformation Technology Act
The Information Technology Act, 2000 (also known as ITA-2000, or the IT Act) is an Act of the Indian Parliament (No 21 of 2000) notified on 17 October 2000. It is the primary law in India dealing with cybercrime and electronic commerce.
Secon ...
of 2008 with no debate, giving the government fiat power to tap all communications without a court order or a warrant. Section 69 of the act states "Section 69 empowers the Central Government/State Government/ its authorized agency to intercept, monitor or decrypt any information generated, transmitted, received or stored in any computer resource if it is necessary or expedient so to do in the interest of the sovereignty or integrity of India, defence of India, security of the State, friendly relations with foreign States or public order or for preventing incitement to the commission of any cognizable offence or for investigation of any offence."
India is setting up a national intelligence grid called NATGRID
The National Intelligence Grid or NATGRID is the integrated intelligence master database structure for counter-terrorism purpose connecting databases of various core security agencies under Government of India collecting comprehensive patterns pr ...
, which would be fully set up by May 2011 where each individual's data ranging from land records, Internet logs, air and rail PNR, phone records, gun records, driving license, property records, insurance, and income tax records would be available in real time and with no oversight. With a UID from the Unique Identification Authority of India
Aadhaar ( hi, आधार, ādhār, lit=base, foundation, bn, আধার) is a 12-digit unique identity number that can be obtained voluntarily by the citizens of India and resident foreign nationals who have spent over 182 days in twelve ...
being given to every Indian from February 2011, the government would be able track people in real time. A national population registry of all citizens will be established by the 2011 census, during which fingerprints and iris scans would be taken along with GPS records of each household.
As per the initial plan, access to the combined data will be given to 11 agencies, including the Research and Analysis Wing, the Intelligence Bureau, the Enforcement Directorate
The Directorate of Enforcement (ED) is a law enforcement agency and economic intelligence agency responsible for enforcing economic laws and fighting economic crime in India. It is part of the Department of Revenue, Ministry of Finance, Gover ...
, the National Investigation Agency
The National Investigation Agency (NIA) is the primary counter-terrorist task force of India. The agency is empowered to deal with the investigation of terror related crimes across states without special permission from the states under written ...
, the Central Bureau of Investigation, the Directorate of Revenue Intelligence
The Directorate of Revenue Intelligence (DRI) is an Indian intelligence agency. It is India's apex anti-smuggling intelligence, investigations and operations agency.
The Directorate is run by officers from the Central Board of Indirect Taxes a ...
and the Narcotics Control Bureau
The Narcotics Control Bureau ( NCB) is an Indian central law enforcement and intelligence agency under the Ministry of Home Affairs, Government of India. The agency is tasked with combating drug trafficking and the use of illegal substance ...
.
Several states within India have already installed CCTV surveillance systems with face matching capabilities using biometrics in Aadhaar. Andhra Pradesh and Telangana are using information linked with Aadhaar across different agencies to create a 360-degree profile of a person, calling it the Integration Information Hub. Other states are now planning to follow this model.
Iran
Iran
Iran, officially the Islamic Republic of Iran, and also called Persia, is a country located in Western Asia. It is bordered by Iraq and Turkey to the west, by Azerbaijan and Armenia to the northwest, by the Caspian Sea and Turkmeni ...
is one of the five countries on Reporters Without Borders' March 2013 list of "State Enemies of the Internet", countries whose governments are involved in naturally active efforts to news providers . The government runs or controls almost all of the country's institutions for regulating, managing or legislating on telecommunications. The Supreme Council for Cyberspace, which was headed by President Ahmadinejad
Mahmoud Ahmadinejad ( fa, محمود احمدینژاد, Mahmūd Ahmadīnežād ), born Mahmoud Sabbaghian ( fa, محمود صباغیان, Mahmoud Sabbāghyān, 28 October 1956),
, was established in March 2012 and now determines digital policy. The construction of a parallel "Iranian Internet", with a high connection speed but fully monitored and censored, is almost complete.
The tools used by the Iranian authorities to monitor and control the Internet include data interception tools capable of Deep Packet Inspection
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is oft ...
. Interception products from leading Chinese companies such as ZTE
ZTE Corporation is a Chinese partially state-owned technology company that specializes in telecommunication. Founded in 1985, ZTE is listed on both the Hong Kong and Shenzhen Stock Exchanges.
ZTE's core business is wireless, exchange, opt ...
and Huawei
Huawei Technologies Co., Ltd. ( ; ) is a Chinese multinational technology corporation headquartered in Shenzhen, Guangdong, China. It designs, develops, produces and sells telecommunications equipment, consumer electronics and various smar ...
are in use. The products provided by Huawei to Mobin Net, the leading national provider of mobile broadband, can be used to analyze email content, track browsing history and block access to sites. The products that ZTA sold to the Telecommunication Company of Iran
Telecommunication Company of Iran, or TCI ( fa, شرکت مخابرات ایران, romanized: ''Sherkat-e Moxaberat-e Iran''), is the fixed-line incumbent operator in Iran offering services in fixed telephony, DSL and data services for both resi ...
(TCI) offer similar services plus the possibility of monitoring the mobile network. European companies are the source of other spying and data analysis tools. Products designed by Ericsson
(lit. "Telephone Stock Company of LM Ericsson"), commonly known as Ericsson, is a Swedish multinational networking and telecommunications company headquartered in Stockholm. The company sells infrastructure, software, and services in informa ...
and Nokia Siemens Networks
Nokia Networks (formerly Nokia Solutions and Networks (NSN) and Nokia Siemens Networks (NSN)) is a multinational data networking and telecommunications equipment company headquartered in Espoo, Finland, and wholly owned subsidiary of Nokia Corp ...
(later Trovicor) are in use. These companies sold SMS
Short Message/Messaging Service, commonly abbreviated as SMS, is a text messaging service component of most telephone, Internet and mobile device systems. It uses standardized communication protocols that let mobile devices exchange short text ...
interception and user location products to Mobile Communication Company of Iran and Irancell
Irancell is an Iranian telecommunications company that operates Iran's largest 2G-3G-4G-4.5G-5G mobile network, and fixed wireless TD-LTE internet services. It is the first provider of 5G internet in Iran. As of 2013, Irancell holds a revenue of ...
, Iran's two biggest mobile phone companies, in 2009 and they were used to identify Iranian citizens during the post-election uprising in 2009. The use of Israeli surveillance devices has also been detected in Iran. The network traffic management and surveillance device NetEnforcer was provided by Israel to Denmark and then resold to Iran. Similarly, US equipment has found its way to Iran via the Chinese company ZTE.
Malaysia
In July 2018, the Malaysian police announced the creation of the Malaysian Intercept Crimes Against Children Unit (icacu) that is equipped with real-time mass internet surveillance software developed in the United States and is tasked with the monitoring of all Malaysian internet users, with a focus on pornography and child pornography. The system creates a "data library" of users which includes details such as IP addresses, websites, locations, duration and frequency of use and files uploaded and downloaded.Mexico
After struggling with drug trafficking and criminal groups for decades Mexico has been strengthening their military mass surveillance. Approximately half of the population in Mexico does not support democracy as a form of government, and believe an authoritarian system is better if social matters are solved through it. The relevance of these political beliefs may make it easier for mass surveillance to spread within the country. "This does not necessarily mean the end of democratic institutions as a whole—such as free elections or the permanence of critical mass media—but it means strengthening the mechanisms for exercising power that exclude dialogue, transparency and social agreement." Developing intelligence agencies has been on Mexico's radar for a while for means of security.Netherlands
According to a 2004 report, the government of the Netherlands carries out more clandestine wire-taps and intercepts than any country, per capita, in the world."Italy and the Netherlands top wiretap chart"Digital Civil Rights in Europe, EDRI-gram Number 2.14, 15 July 2004. Retrieved 17 September 2013. The Dutch military intelligence service MIVD operates a satellite ground station to intercept foreign satellite links and also a facility to eavesdrop on foreign high-frequency radio traffic. An example of mass surveillance carried out by corporations in the Netherlands is an initiative started by five Dutch banks (ABN AMRO, ING, Rabobank, Triodos Bank and de Volksbank). In July 2020 these five banks have decided to establish Transaction Monitoring Netherlands (TMNL) in the collective fight against money laundering and the financing of terrorism. The goal of TMNL-organization is to gather all transaction information provided by Dutch banks in a centralized database to enable full-scale collective transaction monitoring. Preparations have been started but the actual monitoring by TMNL can start after an amendment of the Dutch Anti-Money Laundering and Anti-Terrorist Financing Act.
North Korea
Having attained the nickname 'surveillance state', North Korea's government has complete control over all forms of telecommunications and Internet. It is routine to be sent to a prison camp for communicating with the outside world. The government enforces restrictions around the types of appliances North Koreans may own in their home, in case radio or TV sets pick up signals from nearby South Korea, China and Russia. There is no attempt to mask the way this government actively spies on their citizens. In North Korea, an increasing number of citizens do have smartphones. However, these devices are heavily controlled and are being used to censor and observe everything North Koreans do on their phones. Reuters reported in 2015 that Koryolink, North Korea's official mobile phone network, has around 3 million subscribers in a country of 24 million. Obviously, in order to have digital data to draw from, the citizens must have access to phones and other things online.Russia
TheSORM
The System for Operative Investigative Activities (SORM; russian: Система оперативно-разыскных мероприятий) is the technical specification for lawful interception interfaces of telecommunications and telephone n ...
(and SORM-2) laws enable complete monitoring of any communication
Communication (from la, communicare, meaning "to share" or "to be in relation with") is usually defined as the transmission of information. The term may also refer to the message communicated through such transmissions or the field of inquir ...
, electronic
Electronic may refer to:
*Electronics, the science of how to control electric energy in semiconductor
* ''Electronics'' (magazine), a defunct American trade journal
*Electronic storage, the storage of data using an electronic device
*Electronic co ...
or traditional, by eight state agencies, without warrant. These laws seem to be in conflict with Article 23 of the Constitution of Russia
The Constitution of the Russian Federation () was adopted by national referendum on 12 December 1993. Russia's constitution came into force on 25 December 1993, at the moment of its official publication, and abolished the Soviet system of gov ...
which states:"Chapter 2. Rights and Freedoms of Man And Citizen"''Constitution of Russia''. Retrieved 17 September 2013.
# Everyone shall have the right to the inviolability of private life, personal and family secrets, the protection of honour and good name. # Everyone shall have the right to privacy of correspondence, of telephone conversations, postal, telegraph and other messages. Limitations of this right shall be allowed only by court decision.In 2015, the
European Court for Human Rights
The European Court of Human Rights (ECHR or ECtHR), also known as the Strasbourg Court, is an international court of the Council of Europe which interprets the European Convention on Human Rights. The court hears applications alleging that a c ...
ruled that the legislation violated Article 8 of the European Convention on Human Rights Article 8 of the European Convention on Human Rights provides a right to respect for one's "private and family life, his home and his correspondence", subject to certain restrictions that are "in accordance with law" and " necessary in a democrati ...
(''Zakharov v. Russia
''Zakharov v. Russia'' was a 2015 court case before the European Court of Human Rights involving Roman Zakharov and the Russian Federation. The Court ruled that Russia's legal provisions governing communications surveillance did not provide adeq ...
'').
СAMERTON: Is a global vehicle tracking system, control and tracking, identification of probable routes and places of the most frequent appearance of a particular vehicle, integrated with a distributed network of radar complexes of photo-video fixation and road surveillance camera. Developed and implemented by th"Advanced Scientific - Research Projects"
enterprise St. Petersburg. Within the framework of the practical use of the system of the Ministry of Internal Affairs of the Russian Federation, it has made it possible to identify and solve grave and especially grave crimes, the system is also operated by other state services and departments;
Singapore
Singapore
Singapore (), officially the Republic of Singapore, is a sovereign island country and city-state in maritime Southeast Asia. It lies about one degree of latitude () north of the equator, off the southern tip of the Malay Peninsula, borde ...
is known as a city of sensors. Singapore's surveillance structure spreads widely from closed-circuit television
Closed-circuit television (CCTV), also known as video surveillance, is the use of video cameras to transmit a signal to a specific place, on a limited set of monitors. It differs from broadcast television in that the signal is not openly t ...
(CCTV) in public areas even around the neighbourhood, internet monitoring/traffic monitoring and to the use of surveillance metadata
Metadata is "data that provides information about other data", but not the content of the data, such as the text of a message or the image itself. There are many distinct types of metadata, including:
* Descriptive metadata – the descriptive ...
for government initiatives. In Singapore, SIM card registration is mandatory even for prepaid card. Singapore's government have the rights to access communication data. Singapore's largest telecompany, Singtel, has close relations to the government and Singapore's laws are broadly phrased to allow the government to obtain sensitive data such as text-messages, email, call logs, and web surfing history from its people without the need for court permission.
The installation of mass surveillance cameras in Singapore is an effort to act as a deterrence not only for terror attacks but also for public security such as loan sharks, illegal parking, and more. As part of Singapore's Smart Nation
The Smart Nation is an initiative by the Government of Singapore to harness infocomm technologies, networks and big data to create tech-enabled solutions.
Overview
The Smart Nation was an initiative launched by Prime Minister Lee Hsien Loong on 24 ...
initiative to build a network of sensors to collect and connect data from city life (including the citizen's movement), the Singapore government rolled out 1000 sensors ranging from computer chips to surveillance cameras, to track almost everything in Singapore from air quality to public safety in 2014.
In 2016, in a bid to increase security, the Singapore Police Force
The Singapore Police Force (SPF) is the national and principal Police, law enforcement agency responsible for the prevention of crime and law enforcement in the Republic of Singapore. It is the country's lead agency against organised crime; huma ...
installed 62,000 police cameras in 10,000 Housing and Development Board
The Housing & Development Board (HDB) (; ms, Lembaga Perumahan dan Pembangunan; ta, வீடமைப்பு வளர்ச்சிக் கழகம்) or often referred to as the Housing Board, is a statutory board under the M ...
(HDB) blocks covering the lifts and multi-storey car parks. With rising security concerns, the number of CCTV cameras in public areas such as monitoring of the public transport system and commercial/ government buildings in Singapore is set to increase.
In 2018, the Singapore government would be rolling out new and more advanced surveillance systems. Starting with Singapore's maritime borders, new panoramic electro-optic sensors will be put in place on the north and south coasts, monitoring a 360-degree view of the area. A tethered unmanned aerial vehicle
An unmanned aerial vehicle (UAV), commonly known as a drone, is an aircraft without any human pilot, crew, or passengers on board. UAVs are a component of an unmanned aircraft system (UAS), which includes adding a ground-based controller ...
(UAV) will also be operational, which can be used during search and rescue operations including hostage situations and public order incidents.
Spain
According to a 2017 report byPrivacy International
Privacy International (PI) is a UK-based registered charity that defends and promotes the right to privacy across the world. First formed in 1990, registered as a non-profit company in 2002 and as a charity in 2012, PI is based in London. Its c ...
, Spain may be part of a group of 21 European countries that is withholding information, also known as data retention. In 2014, many defense lawyers tried to overturn multiple cases that used mass storage as their evidence to convict, according to the European Agency for Fundamental Rights.
Sweden
Prior to 2009, theNational Defence Radio Establishment
The National Defence Radio Establishment ( sv, Försvarets radioanstalt, FRA) is a Swedish
government agency organised under the Ministry of Defence. The two main tasks of FRA are signals intelligence (SIGINT), and support to government authorit ...
(FRA) was limited to wireless signals intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
(SIGINT), although it was left largely unregulated. In December 2009, new legislation went into effect, allowing the FRA to monitor cable bound signals passing the Swedish border. Communications service providers are legally required, under confidentiality, to transfer cable communications crossing Swedish borders to specific "interaction points", where data may be accessed after a court order.
The FRA has been contested since the change in its legislation, mainly because of the public perception the change would enable mass surveillance. The FRA categorically deny this allegation, as they are not allowed to initialize any surveillance on their own, and has no direct access to communication lines. All SIGINT has to be authorized by a special court
An extraordinary court, or special court, is a type of court that is established outside of ordinary judiciary, composed of irregularly selected judges or applies irregular procedure for judgment. Since extraordinary court can be abused to infrin ...
and meet a set of narrow requirements, something Minister for Defence
{{unsourced, date=February 2021
A ministry of defence or defense (see spelling differences), also known as a department of defence or defense, is an often-used name for the part of a government responsible for matters of defence, found in states ...
Sten Tolgfors have been quoted as saying, "should render the debate on mass surveillance invalid". Due to the architecture of Internet backbones in the Nordic area, a large portion of Norwegian and Finnish traffic will also be affected by the Swedish wiretapping.
Syria
Syria
Syria ( ar, سُورِيَا or سُورِيَة, translit=Sūriyā), officially the Syrian Arab Republic ( ar, الجمهورية العربية السورية, al-Jumhūrīyah al-ʻArabīyah as-Sūrīyah), is a Western Asian country loc ...
is one of the five countries on Reporters Without Borders' March 2013 list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and human rights. Syria has stepped up its web censorship and cyber-monitoring as the country's civil war has intensified. At least 13 Blue Coat proxy servers are in use, Skype
Skype () is a proprietary telecommunications application operated by Skype Technologies, a division of Microsoft, best known for VoIP-based videotelephony, videoconferencing and voice calls. It also has instant messaging, file transfer, deb ...
calls are intercepted, and social engineering techniques, phishing
Phishing is a type of social engineering where an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a person into revealing sensitive information to the attacker or to deploy malicious softwa ...
, and malware attacks are all in use.
United Arab Emirates
In October 2016, ''The Intercept
''The Intercept'' is an American left-wing news website founded by Glenn Greenwald, Jeremy Scahill, Laura Poitras and funded by billionaire eBay co-founder Pierre Omidyar. Its current editor is Betsy Reed. The publication initially reporte ...
'' released a report detailing the experience of an Italian security researcher Simone Margaritelli, of allegedly being hired for mass surveillance operations run by United Arab Emirates
The United Arab Emirates (UAE; ar, اَلْإِمَارَات الْعَرَبِيَة الْمُتَحِدَة ), or simply the Emirates ( ar, الِْإمَارَات ), is a country in Western Asia (The Middle East). It is located at th ...
. According to Margaritelli, he was called for an interview with the Abu Dhabi
Abu Dhabi (, ; ar, أَبُو ظَبْيٍ ' ) is the capital and second-most populous city (after Dubai) of the United Arab Emirates. It is also the capital of the Emirate of Abu Dhabi and the centre of the Abu Dhabi Metropolitan Area.
...
-based cybersecurity
Computer security, cybersecurity (cyber security), or information technology security (IT security) is the protection of computer systems and networks from attack by malicious actors that may result in unauthorized information disclosure, t ...
firm called DarkMatter
DarkMatter was an art and activist collaboration between Janani Balasubramanian and Alok Vaid-Menon, known for their spoken word performances and queer/trans South Asian themes.
Background
Balasubramanian and Vaid-Menon, both Indian American, m ...
. Margaritelli says he declined the offer and instead wrote a blog post titled "How the United Arab Emirates Intelligence Tried to Hire Me to Spy on Its People". In response to The Intercept inquiries, DarkMatter responded by stating: "No one from DarkMatter or its subsidiaries have ever interviewed Mr. Margaritelli." Kevin Healy, director of communications for DarkMatter, wrote in an email responding to The Intercept that the man Margaritelli says interviewed him was previously only an advisory consultant to DarkMatter and is currently no longer an advisor to the company. Dark Matter responded by saying "While we respect an author's right to express a personal opinion, we do not view the content in question as credible, and therefore have no further comment."
In January 2019, Reuters
Reuters ( ) is a news agency owned by Thomson Reuters Corporation. It employs around 2,500 journalists and 600 photojournalists in about 200 locations worldwide. Reuters is one of the largest news agencies in the world.
The agency was estab ...
released a detailed account of a 2014 state-surveillance operation – dubbed as Project Raven – led by the United Arab Emirates
The United Arab Emirates (UAE; ar, اَلْإِمَارَات الْعَرَبِيَة الْمُتَحِدَة ), or simply the Emirates ( ar, الِْإمَارَات ), is a country in Western Asia (The Middle East). It is located at th ...
with the help of former NSA
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
officials like Lori Stroud, an ex-NSA cyberspy. Counter-terrorism
Counterterrorism (also spelled counter-terrorism), also known as anti-terrorism, incorporates the practices, military tactics, techniques, and strategies that governments, law enforcement, business, and intelligence agencies use to combat or el ...
strategy was the primary motive of setting up the unit. However, soon the project began being used as a surveillance program to spy on rival leaders, critical dissidents
A dissident is a person who actively challenges an established political or religious system, doctrine, belief, policy, or institution. In a religious context, the word has been used since the 18th century, and in the political sense since the 20th ...
and journalists.
In December 2019, Google Play Store
Google Play, also known as the Google Play Store and formerly the Android Market, is a digital distribution service operated and developed by Google. It serves as the official app store for certified devices running on the Android operating syst ...
and Apple App Store
The App Store is an app store platform, developed and maintained by Apple Inc., for mobile apps on its iOS and iPadOS operating systems. The store allows users to browse and download approved apps developed within Apple's iOS Software Devel ...
removed an Emirati messaging application called ToTok
Totok is an Indonesian term of Javanese origin, used in Indonesia to refer to recent migrants of Arab, Chinese or European origins. In the eighteenth and nineteenth centuries it was popularised among colonists in Batavia, who initially coined ...
following allegations that it was a state surveillance application, according to ''The New York Times
''The New York Times'' (''the Times'', ''NYT'', or the Gray Lady) is a daily newspaper based in New York City with a worldwide readership reported in 2020 to comprise a declining 840,000 paid print subscribers, and a growing 6 million paid ...
'' report. The application's privacy policy clearly stated that it may share personal data of the users with "regulatory agencies, law enforcement, and other lawful access requests". The allegations were denied by the co-founders of ToTok, Giacomo Ziani and Long Ruan, respectively. The application was restored on Google Play Store later on.
In July 2020, the United Arab Emirates came under renewed questions about mass surveillance amidst the coronavirus outbreak. Experts highlighted that the country has one of the highest per capita concentrations of surveillance cameras in the world. In a statement, the Emirati government acknowledged that cameras are used to counter the threat of terrorism and have helped the country rank as one of the safest countries in the world.
United Kingdom
State surveillance in theUnited Kingdom
The United Kingdom of Great Britain and Northern Ireland, commonly known as the United Kingdom (UK) or Britain, is a country in Europe, off the north-western coast of the continental mainland. It comprises England, Scotland, Wales and North ...
has formed part of the public consciousness since the 19th century. The postal espionage crisis of 1844 sparked the first panic over the privacy of citizens. However, in the 20th century, electronic surveillance capabilities grew out of wartime signal intelligence and pioneering code breaking
Cryptanalysis (from the Greek ''kryptós'', "hidden", and ''analýein'', "to analyze") refers to the process of analyzing information systems in order to understand hidden aspects of the systems. Cryptanalysis is used to breach cryptographic sec ...
. In 1946, the Government Communications Headquarters
Government Communications Headquarters, commonly known as GCHQ, is an intelligence and security organisation responsible for providing signals intelligence (SIGINT) and information assurance (IA) to the government and armed forces of the Un ...
(GCHQ) was formed. The United Kingdom and the United States signed the bilateral UKUSA Agreement
The United Kingdom – United States of America Agreement (UKUSA, ) is a multilateral agreement for cooperation in signals intelligence between Australia, Canada, New Zealand, the United Kingdom, and the United States. The alliance of intellig ...
in 1948. It was later broadened to include Canada, Australia and New Zealand, as well as cooperation with several "third-party" nations. This became the cornerstone of Western intelligence gathering and the " Special Relationship" between the UK and the US.
After the growth of the Internet and development of the World Wide Web
The World Wide Web (WWW), commonly known as the Web, is an information system enabling documents and other web resources to be accessed over the Internet.
Documents and downloadable media are made available to the network through web se ...
, a series of media reports in 2013 revealed more recent programs and techniques involving GCHQ, such as Tempora
Tempora is the codeword for a formerly-secret computer system that is used by the British Government Communications Headquarters (GCHQ). This system is used to buffer most Internet communications that are extracted from fibre-optic cables, so t ...
.
The use of these capabilities is controlled by laws made in the UK Parliament
The Parliament of the United Kingdom is the supreme legislative body of the United Kingdom, the Crown Dependencies and the British Overseas Territories. It meets at the Palace of Westminster, London. It alone possesses legislative supremac ...
. In particular, access to the content of private messages (that is, interception of a communication) must be authorized by a warrant signed by a Secretary of State. In addition European Union data privacy
Information privacy is the relationship between the collection and dissemination of data, technology, the public expectation of privacy, contextual information norms, and the legal and political issues surrounding them. It is also known as data pr ...
law applies in UK law. The UK exhibits governance and safeguards as well as use of electronic surveillance.
The Investigatory Powers Tribunal
In the United Kingdom, the Investigatory Powers Tribunal (IPT) is a judicial body, independent of the British government, which hears complaints about surveillance by public bodies—in fact, "the only Tribunal to whom complaints about the Intel ...
, a judicial oversight body for the intelligence agencies, ruled in December 2014 that the legislative framework in the United Kingdom does not breach the European Convention on Human Rights
The European Convention on Human Rights (ECHR; formally the Convention for the Protection of Human Rights and Fundamental Freedoms) is an international convention to protect human rights and political freedoms in Europe. Drafted in 1950 by t ...
. However, the Tribunal stated in February 2015 that one particular aspect, the data sharing
Data sharing is the practice of making data used for scholarly research available to other investigators. Many funding agencies, institutions, and publication venues have policies regarding data sharing because transparency and openness are consid ...
arrangement that allowed UK Intelligence services to request data from the US surveillance programs Prism
Prism usually refers to:
* Prism (optics), a transparent optical component with flat surfaces that refract light
* Prism (geometry), a kind of polyhedron
Prism may also refer to:
Science and mathematics
* Prism (geology), a type of sedimentary ...
and Upstream
Upstream may refer to:
* Upstream (bioprocess)
* ''Upstream'' (film), a 1927 film by John Ford
* Upstream (networking)
* ''Upstream'' (newspaper), a newspaper covering the oil and gas industry
* Upstream (petroleum industry)
* Upstream (software ...
, had been in contravention of human rights law prior to this until two paragraphs of additional information, providing details about the procedures and safeguards, were disclosed to the public in December 2014.
In its December 2014 ruling, the Investigatory Powers Tribunal found that the legislative framework in the United Kingdom does not permit mass surveillance and that while GCHQ collects and analyses data in bulk, it does not practice mass surveillance. A report on Privacy and Security published by the Intelligence and Security Committee of Parliament
The Intelligence and Security Committee of Parliament (ISC) is a statutory joint committee of the Parliament of the United Kingdom, appointed to oversee the work of the UK intelligence community.
The committee was established in 1994 by the ...
also came to this view, although it found past shortcomings in oversight and said the legal framework should be simplified to improve transparency. This view is supported by independent reports from the Interception of Communications Commissioner
The Interception of Communications Commissioner was a regulatory official in the United Kingdom, appointed under section 57 of the Regulation of Investigatory Powers Act 2000, and previously under section 8 of the Interception of Communications ...
. However, notable civil liberties groups continue to express strong views to the contrary and plan to appeal the ruling to the European Court of Human Rights
The European Court of Human Rights (ECHR or ECtHR), also known as the Strasbourg Court, is an international court of the Council of Europe which interprets the European Convention on Human Rights. The court hears applications alleging that a ...
, while others have criticised these viewpoints in turn.;
 The
The Regulation of Investigatory Powers Act 2000
The Regulation of Investigatory Powers Act 2000 ( c.23) (RIP or RIPA) is an Act of the Parliament of the United Kingdom, regulating the powers of public bodies to carry out surveillance and investigation, and covering the interception of comm ...
(RIP or RIPA) is a significant piece of legislation that granted and regulated the powers of public bodies to carry out surveillance and investigation."Regulation of Investigatory Powers Act 2000"2000 Chapter 23, UK Government Legislation. Retrieved 28 September 2013. In 2002 the UK government announced plans to extend the Regulation of Investigatory Powers Act so that at least 28 government departments would be given powers to access
metadata
Metadata is "data that provides information about other data", but not the content of the data, such as the text of a message or the image itself. There are many distinct types of metadata, including:
* Descriptive metadata – the descriptive ...
about citizens' web, e-mail, telephone and fax records, without a warrant and without a subject's knowledge.
The Protection of Freedoms Act 2012
The Protection of Freedoms Act 2012 is an Act of the Parliament of the United Kingdom. As the Protection of Freedoms Bill, it was introduced in February 2011, by the Home Secretary, Theresa May. The bill was sponsored by the Home Office. On Tuesd ...
includes several provisions related to controlling and restricting the collection, storage, retention, and use of information in government databases."Protection of Freedoms Bill"Home Office, 11 February 2011. Retrieved 28 September 2013. Supported by all three major political parties, the UK Parliament passed the
Data Retention and Investigatory Powers Act
The Data Retention and Investigatory Powers Act 2014 (also known as DRIP or DRIPA) was an Act of the Parliament of the United Kingdom, repealed in 2016. It received Royal Assent on 17 July 2014, after being introduced on 14 July 2014. The purpos ...
in July 2014 to ensure police and security services retain existing powers to access phone and Internet records.
This was superseded by the Investigatory Powers Act 2016
The Investigatory Powers Act 2016 (c. 25) (nicknamed the Snoopers' Charter) is an Act of the Parliament of the United Kingdom which received royal assent on 29 November 2016. Its different parts came into force on various dates from 30 December 2 ...
, a comprehensive statute which made public a number of previously secret powers (equipment interference, bulk retention of metadata, intelligence agency use of bulk personal datasets), and enables the Government to require internet service providers and mobile phone companies to maintain records of (but not the content of) customers' Internet connections for 12 months. In addition, it created new safeguards, including a requirement for judges to approve the warrants authorised by a Secretary of State before they come into force. The Act was informed by two reports by David Anderson QC, the UK's Independent Reviewer of Terrorism Legislation The Independent Reviewer of Terrorism Legislation is an independent person, appointed by the Home Secretary and by the Treasury for a renewable three-year term and tasked with reporting to the Home Secretary and to Parliament on the operation of cou ...
: A Question of Trust (2015) and the report of his Bulk Powers Review (2016), which contains a detailed appraisal (with 60 case studies) of the operational case for the powers often characterised as mass surveillance. It may yet require amendment as a consequence of legal cases brought before the Court of Justice of the European Union
The Court of Justice of the European Union (CJEU) (french: Cour de justice de l'Union européenne or "''CJUE''"; Latin: Curia) is the judicial branch of the European Union (EU). Seated in the Kirchberg quarter of Luxembourg City, Luxembour ...
and the European Court of Human Rights
The European Court of Human Rights (ECHR or ECtHR), also known as the Strasbourg Court, is an international court of the Council of Europe which interprets the European Convention on Human Rights. The court hears applications alleging that a ...
.
Many advanced nation-states have implemented laws that partially protect citizens from unwarranted intrusion, such as the Human Rights Act 1998, the Data Protection Act 1998, (updated as the Data Protection Act 2018
The Data Protection Act 2018 (c. 12) is a United Kingdom Act of Parliament which updates data protection laws in the UK. It is a national law which complements the European Union's General Data Protection Regulation (GDPR) and replaces the Data P ...
, to include the General Data Protection Regulation), and the Privacy and Electronic Communications (EC Directive) Regulations 2003
The Privacy and Electronic Communications (EC Directive) Regulations 2003 is a law in the United Kingdom which made it unlawful to, amongst other things, transmit an automated recorded message for direct marketing purposes via a telephone, without ...
in the United Kingdom, and laws that require a formal warrant before private data may be gathered by a government.
The vast majority of video surveillance cameras in the UK are not operated by government bodies, but by private individuals or companies, especially to monitor the interiors of shops and businesses. According to 2011 Freedom of Information Act Freedom of Information Act may refer to the following legislations in different jurisdictions which mandate the national government to disclose certain data to the general public upon request:
* Freedom of Information Act 1982, the Australian act
* ...
requests, the total number of local government operated CCTV cameras was around 52,000 over the entirety of the UK. The prevalence of video surveillance in the UK is often overstated due to unreliable estimates being requoted; for example one report in 2002 extrapolated from a very small sample to estimate the number of cameras in the UK at 4.2 million (of which 500,000 in London). More reliable estimates put the number of private and local government operated cameras in the United Kingdom at around 1.85 million in 2011.
United States
Historically, mass surveillance was used as part of wartime censorship to control communications that could damage the war effort and aid the enemy. For example, during the world wars, every international telegram from or to the United States sent through companies such asWestern Union
The Western Union Company is an American multinational financial services company, headquartered in Denver, Colorado.
Founded in 1851 as the New York and Mississippi Valley Printing Telegraph Company in Rochester, New York, the company cha ...
was reviewed by the US military. After the wars were over, surveillance continued in programs such as the Black Chamber
The Black Chamber (1919–1929), also known as the Cipher Bureau, was the United States' first peacetime cryptanalytic organization, and a forerunner of the National Security Agency. The only prior codes and cypher organizations maintained by th ...
following World War I and project Shamrock
Project SHAMROCK was the sister project to Project MINARET, an espionage exercise started in August 1945. Project MINARET involved the accumulation of all telegraphic data that entered or exited the United States. The Armed Forces Security Agency ...
following World War II. COINTELPRO
COINTELPRO (syllabic abbreviation derived from Counterintelligence, Counter Intelligence Program; 1956–1971) was a series of Covert operation, covert and illegal projects actively conducted by the United States Federal Bureau of Investigation ( ...
projects conducted by the U.S. Federal Bureau of Investigation (FBI) between 1956 and 1971 targeted various "subversive" organizations, including peaceful anti-war and racial equality activists such as Albert Einstein
Albert Einstein ( ; ; 14 March 1879 – 18 April 1955) was a German-born theoretical physicist, widely acknowledged to be one of the greatest and most influential physicists of all time. Einstein is best known for developing the theory ...
and Martin Luther King Jr.
Martin Luther King Jr. (born Michael King Jr.; January 15, 1929 – April 4, 1968) was an American Baptist minister and activist, one of the most prominent leaders in the civil rights movement from 1955 until his assassination in 1968 ...
Billions of dollars per year are spent, by agencies such as the National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
(NSA) and the Federal Bureau of Investigation
The Federal Bureau of Investigation (FBI) is the domestic intelligence and security service of the United States and its principal federal law enforcement agency. Operating under the jurisdiction of the United States Department of Justice, ...
(FBI), to develop, purchase, implement, and operate systems such as Carnivore
A carnivore , or meat-eater (Latin, ''caro'', genitive ''carnis'', meaning meat or "flesh" and ''vorare'' meaning "to devour"), is an animal or plant whose food and energy requirements derive from animal tissues (mainly muscle, fat and other sof ...
, ECHELON, and NarusInsight
Narus Inc. was a Software industry, software company and Independent software vendor, vendor of big data analytics for cybersecurity.
History
In 1997, Ori Cohen, Vice President of Business and Technology Development for VDONet, founded Narus with ...
to intercept and analyze the immense amount of data that traverses the Internet and telephone system every day.
Under the Mail Isolation Control and Tracking Mail Isolation Control and Tracking (MICT) is an imaging system employed by the United States Postal Service (USPS) that takes photographs of the exterior of every piece of mail that is processed in the United States. The Postmaster General has stat ...
program, the U.S. Postal Service photographs the exterior of every piece of paper mail that is processed in the United States – about 160 billion pieces in 2012. The U.S. Postmaster General stated that the system is primarily used for mail sorting, but the images are available for possible use by law enforcement agencies."AP Interview: USPS takes photos of all mail", Associated Press (AP), 2 August 2013. Created in 2001 following the anthrax attacks that killed five people, it is a sweeping expansion of a 100-year-old program called "
mail cover
Mail cover is a law enforcement investigative technique in which the United States Postal Service, acting at the request of a law enforcement agency, records information from the outside of letters and parcels before they are delivered and then se ...
" which targets people suspected of crimes."U.S. Postal Service Logging All Mail for Law Enforcement"Ron Nixon, ''The New York Times'', 3 July 2013. Retrieved 25 September 2013. The FBI developed the computer programs "
Magic Lantern
The magic lantern, also known by its Latin name , is an early type of image projector that used pictures—paintings, prints, or photographs—on transparent plates (usually made of glass), one or more lenses, and a light source. Because a si ...
" and CIPAV
The Computer and Internet Protocol Address Verifier (CIPAV) is a data gathering tool that the Federal Bureau of Investigation (FBI) uses to track and gather location data on suspects under electronic surveillance. The software operates on the targ ...
, which they can remotely install on a computer system, in order to monitor a person's computer activity.
The NSA has been gathering information on financial records, Internet surfing habits, and monitoring e-mails. They have also performed extensive analysis of social networks
A social network is a social structure made up of a set of social actors (such as individuals or organizations), sets of dyadic ties, and other social interactions between actors. The social network perspective provides a set of methods for a ...
such as Myspace.
The PRISM
Prism usually refers to:
* Prism (optics), a transparent optical component with flat surfaces that refract light
* Prism (geometry), a kind of polyhedron
Prism may also refer to:
Science and mathematics
* Prism (geology), a type of sedimentary ...
special source operation system legally immunized private companies that cooperate voluntarily with U.S. intelligence collection. According to ''The Register'', the FISA Amendments Act of 2008
The FISA Amendments Act of 2008, also called the FAA and Foreign Intelligence Surveillance Act of 1978 Amendments Act of 2008, is an Act of Congress that amended the Foreign Intelligence Surveillance Act. It has been used as the legal basis fo ...
"specifically authorizes intelligence agencies to monitor the phone, email, and other communications of U.S. citizens for up to a week without obtaining a warrant" when one of the parties is outside the U.S. PRISM was first publicly revealed on 6 June 2013, after classified documents about the program were leaked to ''The Washington Post'' and ''The Guardian'' by American Edward Snowden
Edward Joseph Snowden (born June 21, 1983) is an American and naturalized Russian former computer intelligence consultant who leaked highly classified information from the National Security Agency (NSA) in 2013, when he was an employee and su ...
.
The Communications Assistance for Law Enforcement Act
The Communications Assistance for Law Enforcement Act (CALEA), also known as the "Digital Telephony Act," is a United States wiretapping law passed in 1994, during the presidency of Bill Clinton (Pub. L. No. 103-414, 108 Stat. 4279, codified at 47 ...
(CALEA) requires that all U.S. telecommunications and Internet service providers modify their networks to allow easy wiretapping
Telephone tapping (also wire tapping or wiretapping in American English) is the monitoring of telephone and Internet-based conversations by a third party, often by covert means. The wire tap received its name because, historically, the monitorin ...
of telephone, VoIP, and broadband Internet traffic.
In early 2006, ''USA Today
''USA Today'' (stylized in all uppercase) is an American daily middle-market newspaper and news broadcasting company. Founded by Al Neuharth on September 15, 1982, the newspaper operates from Gannett's corporate headquarters in Tysons, Virgini ...
'' reported that several major telephone companies were providing the telephone call records of U.S. citizens to the National Security Agency
The National Security Agency (NSA) is a national-level intelligence agency of the United States Department of Defense, under the authority of the Director of National Intelligence (DNI). The NSA is responsible for global monitoring, collecti ...
(NSA), which is storing them in a large database known as the NSA call database
MAINWAY is a database maintained by the United States' National Security Agency (NSA) containing metadata for hundreds of billions of telephone calls made through the largest telephone carriers in the United States, including AT&T, Verizon, and ...
. This report came on the heels of allegations that the U.S. government had been conducting electronic surveillance of domestic telephone calls without warrants. In 2013, the existence of the Hemisphere Project
The Hemisphere Project, also called simply Hemisphere (codename ''Hudson Hawk''), is a mass surveillance program conducted by US telephone company AT&T and paid for by the White House Office of National Drug Control Policy and the Drug Enforcement ...
, through which AT&T provides telephone call data to federal agencies, became publicly known.
Traffic cameras, which were meant to help enforce traffic laws at intersections, may be used by law enforcement agencies for purposes unrelated to traffic violations. Some cameras allow for the identification of individuals inside a vehicle and license plate data to be collected and time stamped for cross reference with other data used by police. The Department of Homeland Security
The United States Department of Homeland Security (DHS) is the U.S. federal executive department responsible for public security, roughly comparable to the interior or home ministries of other countries. Its stated missions involve anti-terr ...
is funding networks of surveillance cameras in cities and towns as part of its efforts to combat terrorism.
The New York City Police Department
The New York City Police Department (NYPD), officially the City of New York Police Department, established on May 23, 1845, is the primary municipal law enforcement agency within the City of New York, the largest and one of the oldest in ...
infiltrated and compiled dossiers on protest groups before the 2004 Republican National Convention, leading to over 1,800 arrests.
Modern surveillance in the United States was thought of more of a wartime effort before Snowden disclosed in depth information about the National Security Agency in June 2013.van der Vlist, Fernando N. 2017. Counter-Mapping Surveillance: A Critical Cartography of Mass Surveillance Technology After Snowden. Surveillance & Society 15(1): 137-157. The constant development and improvements of the Internet and technology has made it easier for mass surveillance to take hold. Such revelations allow critical commentators to raise questions and scrutinize the implementation, use, and abuse of networking technologies, devices, and software systems that partake in a "global surveillant assemblage" (Bogard 2006; Collier and Ong 2004; Haggerty and Ericson 2000; Murakami Wood 2013). The NSA collected millions of Verizon user's telephone records in between 2013 and 2014. The NSA also collected data through Google and Facebook with a program called 'Prism'. Journalists through Snowden published nearly 7,000 top-secret documents since then, yet the information disclosed seems to be less than 1% of the entire information. Having access to every individual's private records seems to directly contradict the fourth amendment.
Vietnam
Vietnam
Vietnam or Viet Nam ( vi, Việt Nam, ), officially the Socialist Republic of Vietnam,., group="n" is a country in Southeast Asia, at the eastern edge of mainland Southeast Asia, with an area of and population of 96 million, making i ...
is one of the five countries on Reporters Without Borders' March 2013 list of "State Enemies of the Internet", countries whose governments are involved in active, intrusive surveillance of news providers, resulting in grave violations of freedom of information and human rights. Most of the country's 16 service providers are directly or indirectly controlled by the Vietnamese Communist Party
The Communist Party of Vietnam (CPV), also known as the Vietnamese Communist Party (VCP), is the founding and sole legal party of the Socialist Republic of Vietnam. Founded in 1930 by Hồ Chí Minh, the CPV became the ruling party of North ...
. The industry leader, Vietnam Posts and Telecommunications Group
Vietnam Posts and Telecommunications Group (VNPT, ), is a telecommunications company, owned by the Government of Vietnam, Vietnamese Government, and the national post office of Vietnam. According to a list of UNDP in 2007, it is the second-lar ...
, which controls 74 per cent of the market, is state-owned. So is Viettel
The Viettel Military Industry and Telecoms Group (), less formally recognized as Viettel Group () or simply Viettel, is a Vietnamese multinational telecommunications company headquartered in Hanoi, Vietnam. Viettel is the largest telecommuni ...
, an enterprise of the Vietnamese armed forces. FPT Telecom is a private firm, but is accountable to the Party and depends on the market leaders for bandwidth.
Service providers are the major instruments of control and surveillance. Bloggers monitored by the government frequently undergo man-in-the-middle attack
In cryptography and computer security, a man-in-the-middle, monster-in-the-middle, machine-in-the-middle, monkey-in-the-middle, meddler-in-the-middle, manipulator-in-the-middle (MITM), person-in-the-middle (PITM) or adversary-in-the-middle (AiTM) ...
s. These are designed to intercept data meant to be sent to secure (https) sites, allowing passwords and other communication to be intercepted. According to a July 2012 Freedom House
Freedom House is a non-profit, majority U.S. government funded organization in Washington, D.C., that conducts research and advocacy on democracy, political freedom, and human rights. Freedom House was founded in October 1941, and Wendell Wil ...
report, 91 percent of survey respondents connected to the Internet on their mobile devices believe that the government monitors conversations and tracks the calls of "activists" or "reactionaries." In 2018, the Vietnam National Assembly also passed a cybersecurity law closely resembling one passed in China, requiring localisation of user data and censorship of anti-state content.
Commercial mass surveillance
As a result of the digital revolution, many aspects of life are now captured and stored in digital form. Concern has been expressed that governments may use this information to conduct mass surveillance on their populations. Commercial mass surveillance often makes use ofcopyright
A copyright is a type of intellectual property that gives its owner the exclusive right to copy, distribute, adapt, display, and perform a creative work, usually for a limited time. The creative work may be in a literary, artistic, education ...
laws and " user agreements" to obtain (typically uninformed) 'consent' to surveillance from consumers who use their software or other related materials. This allows gathering of information which would be technically illegal if performed by government agencies. This data is then often shared with government agencies, thereby, in practice, defeating the purpose of such privacy protections.
One of the most common forms of mass surveillance is carried out by commercial organizations. Many people are willing to join supermarket and grocery loyalty card programs, trading their personal information and surveillance of their shopping habits in exchange for a discount on their groceries, although base prices might be increased to encourage participation in the program.
Through programs like Google
Google LLC () is an American multinational technology company focusing on search engine technology, online advertising, cloud computing, computer software, quantum computing, e-commerce, artificial intelligence, and consumer electronics. ...
's AdSense
Google AdSense is a program run by Google through which website publishers in the Google Network of content sites serve text, images, video, or interactive media advertisements that are targeted to the site content and audience. These advert ...
, OpenSocial
OpenSocial is a public specification that defines a component hosting environment (container) and a set of common application programming interfaces (APIs) for web applications. Initially, it was designed for social network applications and d ...
and their increasing pool of so-called "web gadgets", "social gadgets", and other Google-hosted services many web sites on the Internet are effectively feeding user information about sites visited by the users, and now also their social connections, to Google. Facebook
Facebook is an online social media and social networking service owned by American company Meta Platforms. Founded in 2004 by Mark Zuckerberg with fellow Harvard College students and roommates Eduardo Saverin, Andrew McCollum, Dustin M ...
also keep this information, although its acquisition is limited to page views within Facebook. This data is valuable for authorities, advertisers and others interested in profiling users, trends and web site marketing performance. Google, Facebook and others are increasingly becoming more guarded about this data as their reach increases and the data becomes more all inclusive, making it more valuable.
New features like geolocation
Geopositioning, also known as geotracking, geolocalization, geolocating, geolocation, or geoposition fixing, is the process of determining or estimating the geographic position of an object.
Geopositioning yields a set of geographic coordinates ...
give an even increased admission of monitoring capabilities to large service providers like Google, where they also are enabled to track one's physical movements while users are using mobile devices, especially those which are syncing without any user interaction. Google's Gmail
Gmail is a free email service provided by Google. As of 2019, it had 1.5 billion active users worldwide. A user typically accesses Gmail in a web browser or the official mobile app. Google also supports the use of email clients via the POP and ...
service is increasingly employing features to work as a stand-alone application which also might activate while a web browser is not even active for synchronizing; a feature mentioned on the Google I/O
Google I/O (or simply I/O) is an annual developer conference held by Google in Mountain View, California. "I/O" stands for Input/Output, as well as the slogan "Innovation in the Open". The event's format is similar to Google Developer Day.
Hi ...
2009 developer conference while showing the upcoming HTML5
HTML5 is a markup language used for structuring and presenting content on the World Wide Web. It is the fifth and final major HTML version that is a World Wide Web Consortium (W3C) recommendation. The current specification is known as the HTML ...
features which Google and others are actively defining and promoting.
In 2008 at the World Economic Forum
The World Economic Forum (WEF) is an international non-governmental and lobbying organisation based in Cologny, canton of Geneva, Switzerland. It was founded on 24 January 1971 by German engineer and economist Klaus Schwab. The foundation, ...
in Davos, Google CEO Eric Schmidt, said: "The arrival of a truly mobile Web, offering a new generation of location-based advertising, is set to unleash a 'huge revolution'". At the Mobile World Congress in Barcelona on 16 February 2010, Google presented their vision of a new business model for mobile operators and trying to convince mobile operators to embrace location-based service
A location-based service (LBS) is a general term denoting software services which use geographic data and information to provide services or information to users. LBS can be used in a variety of contexts, such as health, indoor object search, en ...
s and advertising. With Google as the advertising provider, it would mean that every mobile operator using their location-based advertising service would be revealing the location of their mobile customers to Google.
Organizations like the Electronic Frontier Foundation
The Electronic Frontier Foundation (EFF) is an international non-profit digital rights group based in San Francisco, California. The foundation was formed on 10 July 1990 by John Gilmore, John Perry Barlow and Mitch Kapor to promote Internet ci ...
are constantly informing users on the importance of privacy, and considerations about technologies like geolocation.
Computer company Microsoft
Microsoft Corporation is an American multinational technology corporation producing computer software, consumer electronics, personal computers, and related services headquartered at the Microsoft Redmond campus located in Redmond, Washing ...
patented in 2011 a product distribution system with a camera or capture device that monitors the viewers that consume the product, allowing the provider to take "remedial action" if the actual viewers do not match the distribution license.
Reporters Without Borders' March 2013 ''Special report on Internet Surveillance'' contained a list of "Corporate Enemies of the Internet", companies that sell products that are liable to be used by governments to violate human rights and freedom of information. The five companies on the initial list were: Amesys (France), Blue Coat Systems
__FORCETOC__
Blue Coat Systems, Inc., was a company that provided hardware, software, and services designed for cybersecurity and network management. In 2016, it was acquired by and folded into Symantec. In 2019 was, as part of Symantec Enterpris ...
(U.S.), Gamma Group
Gamma Group is an Anglo-German technology company that sells surveillance software to governments and police forces around the world. The company has been strongly criticised by human rights organisations for selling its FinFisher software to u ...
(UK and Germany), Hacking Team
HackingTeam was a Milan-based information technology company that sold offensive intrusion and surveillance capabilities to governments, law enforcement agencies and corporations. Its "''Remote Control Systems''" enable governments and corporatio ...
(Italy), and Trovicor (Germany), but the list was not exhaustive and is likely to be expanded in the future.
EFF
EFF or eff may refer to:
Politics
* Economic Freedom Fighters, a South African communist political party
* Economic Freedom Fund, an American political organization
* Election Fighting Fund, a British suffragist organization supporting the ear ...
found that a company by the name of Fog Data Science purchases location data from apps and sells it to the law enforcement agencies in the U.S. without requiring a warrant or a court order.
Surveillance state
A surveillance state is a country where the government engages in pervasive surveillance of large numbers of its citizens and visitors. Such widespread surveillance is usually justified as being necessary fornational security
National security, or national defence, is the security and defence of a sovereign state, including its citizens, economy, and institutions, which is regarded as a duty of government. Originally conceived as protection against military atta ...
, such as to prevent crime or acts of terrorism, but may also be used to stifle criticism of and opposition to the government.
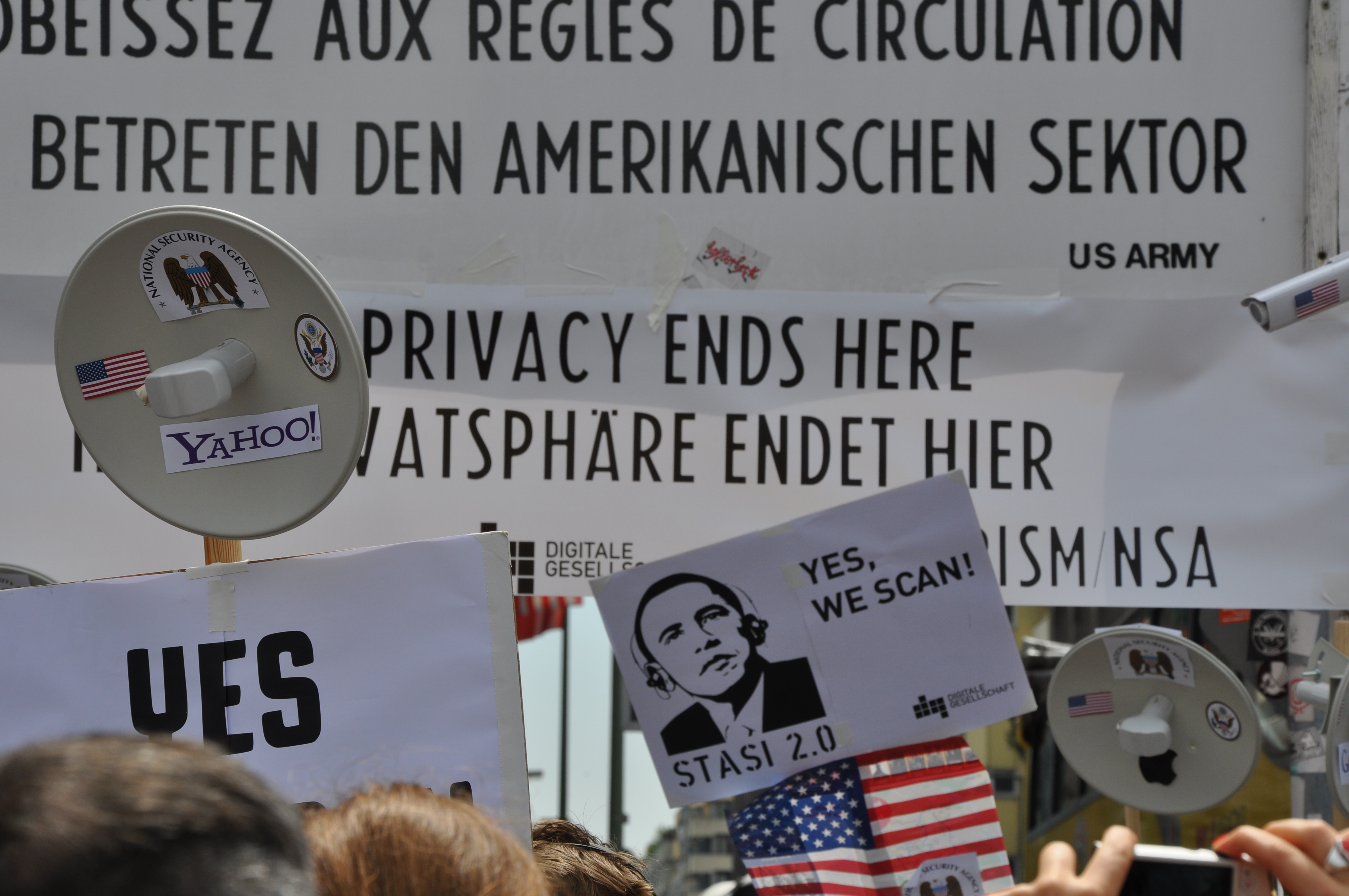 Examples of early surveillance states include the former
Examples of early surveillance states include the former Soviet Union
The Soviet Union,. officially the Union of Soviet Socialist Republics. (USSR),. was a transcontinental country that spanned much of Eurasia from 1922 to 1991. A flagship communist state, it was nominally a federal union of fifteen national ...
and the former East Germany
East Germany, officially the German Democratic Republic (GDR; german: Deutsche Demokratische Republik, , DDR, ), was a country that existed from its creation on 7 October 1949 until its dissolution on 3 October 1990. In these years the state ...
, which had a large network of informers and an advanced technology base in computing and spy-camera technology. However, these states did not have today's technologies for mass surveillance, such as the use of database
In computing, a database is an organized collection of data stored and accessed electronically. Small databases can be stored on a file system, while large databases are hosted on computer clusters or cloud storage. The design of databases sp ...
s and pattern recognition
Pattern recognition is the automated recognition of patterns and regularities in data. It has applications in statistical data analysis, signal processing, image analysis, information retrieval, bioinformatics, data compression, computer graphi ...
software to cross-correlate information obtained by wire tapping
Overhead power cabling. The conductor consists of seven strands of steel (centre, high tensile strength), surrounded by four outer layers of aluminium (high conductivity). Sample diameter 40 mm
A wire is a flexible strand of metal.
Wire is co ...
, including speech recognition
Speech recognition is an interdisciplinary subfield of computer science and computational linguistics that develops methodologies and technologies that enable the recognition and translation of spoken language into text by computers with the m ...
and telecommunications traffic analysis
Traffic analysis is the process of intercepting and examining messages in order to deduce information from patterns in communication, it can be performed even when the messages are encrypted. In general, the greater the number of messages observed ...
, monitoring of financial transactions, automatic number plate recognition
Automatic number-plate recognition (ANPR; see also #Other names, other names below) is a technology that uses optical character recognition on images to read vehicle registration plates to create vehicle location data. It can use existing close ...
, the tracking of the position of mobile telephones, and facial recognition system
A facial recognition system is a technology capable of matching a human face from a digital image or a video frame against a database of faces. Such a system is typically employed to authenticate users through ID verification services, and wo ...
s and the like which recognize people by their appearance, gait, DNA profiling
DNA profiling (also called DNA fingerprinting) is the process of determining an individual's DNA characteristics. DNA analysis intended to identify a species, rather than an individual, is called DNA barcoding.
DNA profiling is a forensic tec ...
, etc.
Smart cities
The development of smart cities has seen the increased adoption of surveillance technologies by governments, although the primary purpose of surveillance in such cities is to use information and communication technologies to control the urban environment. The implementation of such technology by a number of cities has resulted in increased efficiencies in urban infrastructure as well as improved community participation. Sensors and systems monitor a smart city's infrastructure, operations and activities and aim to help it run more efficiently. For example, the city could use less electricity; its traffic run more smoothly with fewer delays; its citizens use the city with more safety; hazards can be dealt with faster; citizen infractions of rules can be prevented, and the city's infrastructure; power distribution and roads with traffic lights for example, dynamically adjusted to respond to differing circumstances. The development of smart city technology has also led to an increase in potential unwarranted intrusions into privacy and restrictions upon autonomy. The widespread incorporation of information and communication technologies within the daily life of urban residents results in increases in the surveillance capacity of states – to the extent that individuals may be unaware of what information is being accessed, when the access occurs and for what purpose. It is possible that such conditions could give rise to the development of an electronic police state. Shanghai, Amsterdam, San Jose, Dubai, Barcelona, Madrid, Stockholm, and New York are all cities that use various techniques from smart city technology.Electronic police state
 An electronic
An electronic police state
A police state describes a state where its government institutions exercise an extreme level of control over civil society and liberties. There is typically little or no distinction between the law and the exercise of political power by the ...
is a state
State may refer to:
Arts, entertainment, and media Literature
* ''State Magazine'', a monthly magazine published by the U.S. Department of State
* ''The State'' (newspaper), a daily newspaper in Columbia, South Carolina, United States
* ''Our S ...
in which the government aggressively uses electronic technologies to record, collect, store, organize, analyze, search, and distribute information about its citizens.The first use of the term "electronic police state" was likely in a posting by Jim Davis The term "electronic police state" became more widely known with the publication o''The Electronic Police State: 2008 National Rankings''
, by Jonathan Logan, Cryptohippie USA. Electronic police states also engage in mass government surveillance of
landline
A landline (land line, land-line, main line, home phone, fixed-line, and wireline) is a telephone connection that uses metal wires or optical fiber telephone line for transmission, as distinguished from a mobile cellular network, which uses ...
and cellular
Cellular may refer to:
*Cellular automaton, a model in discrete mathematics
* Cell biology, the evaluation of cells work and more
* ''Cellular'' (film), a 2004 movie
*Cellular frequencies, assigned to networks operating in cellular RF bands
*Cell ...
telephone traffic, mail, email, web surfing, Internet searches, radio, and other forms of electronic communication as well as widespread use of video surveillance. The information is usually collected in secret.
The crucial elements are not politically based, so long as the government can afford the technology and the populace will permit it to be used, an electronic police state can form. The continual use of electronic mass surveillance can result in constant low-level fear within the population, which can lead to self-censorship
Self-censorship is the act of censoring or classifying one's own discourse. This is done out of fear of, or deference to, the sensibilities or preferences (actual or perceived) of others and without overt pressure from any specific party or insti ...
and exerts a powerful coercive force upon the populace.Kingsley Ufuoma OMOYIBO, Ogaga Ayemo OBARO (2012)"Applications of Social Control Theory: Criminality and Governmentality"
, ''International Journal of Asian Social Science'', Vol. 2, No. 7, pp.1026-1032. Seventeen factors for judging the development of an electronic police state were suggested in ''The Electronic Police State: 2008 National Rankings'': * Daily documents: Requirement for the use and tracking of state-issued identity documents and registration. * Border and travel control: Inspections at borders, searching computers and cell phones, demanding decryption of data, and tracking travel within as well as to and from a country. * Financial tracking: A state's ability to record and search financial transactions: checks, credit cards, wires, etc. * Gag orders: Restrictions on and criminal penalties for the disclosure of the existence of state surveillance programs. * Anti-crypto laws: Outlawing or restricting
cryptography
Cryptography, or cryptology (from grc, , translit=kryptós "hidden, secret"; and ''graphein'', "to write", or ''-logia'', "study", respectively), is the practice and study of techniques for secure communication in the presence of adver ...
and/or privacy enhancing technologies.
* Lack of constitutional protections: A lack of constitutional privacy protections or the routine overriding of such protections.
* Data storage: The ability of the state to store the data gathered.
* Data search: The ability to organize and search the data gathered.
* Data retention requirements: Laws that require Internet and other service providers to save detailed records of their customers' Internet usage for a minimum period of time.
** Telephone data retention requirements: Laws that require telephone companies to record and save records of their customers' telephone usage.
** Cell phone data retention requirements: Laws that require cellular telephone companies to record and save records of their customers' usage and location.
* Medical records: Government access to the records of medical service providers.
* Enforcement: The state's ability to use force to seize anyone they want, whenever they want.
* Lack of ''habeas corpus'': Lack of a right for a person under arrest to be brought before a judge or into court in a timely fashion or the overriding of such rights.
* Lack of a police-intel barrier: The lack of a barrier between police organizations and intelligence organizations, or the overriding of such barriers.
* Covert hacking: State operatives collecting, removing, or adding digital evidence to/from private computers without permission or the knowledge of the computers' owners.
* Loose or no warrants: Arrests or searches made without warrants or without careful examination and review of police statements and justifications by a truly independent judge or other third-party.
The list includes factors that apply to other forms of police states
A police state describes a State (polity), state where its government institutions exercise an extreme level of control over civil society and Liberty, liberties. There is typically little or no distinction between the law and the exercise of p ...
, such as the use of identity documents and police enforcement, but go considerably beyond them and emphasize the use of technology to gather and process the information collected.
In popular culture
 The concept of being monitored by our governments collects a large audience of curious citizens. Mass surveillance has been prominently featured in a wide array of books, films, and other media. Advances in technology over the last century have led to possible social control through the Internet and the conditions of late capitalism. Many directors and writers have been enthralled with the potential stories that could come from mass surveillance. Perhaps the most iconic example of fictional mass surveillance is George Orwell's 1949 novel ''
The concept of being monitored by our governments collects a large audience of curious citizens. Mass surveillance has been prominently featured in a wide array of books, films, and other media. Advances in technology over the last century have led to possible social control through the Internet and the conditions of late capitalism. Many directors and writers have been enthralled with the potential stories that could come from mass surveillance. Perhaps the most iconic example of fictional mass surveillance is George Orwell's 1949 novel ''Nineteen Eighty-Four
''Nineteen Eighty-Four'' (also stylised as ''1984'') is a dystopian social science fiction novel and cautionary tale written by the English writer George Orwell. It was published on 8 June 1949 by Secker & Warburg as Orwell's ninth and fina ...
'', which depicts a dystopia
A dystopia (from Ancient Greek δυσ- "bad, hard" and τόπος "place"; alternatively cacotopiaCacotopia (from κακός ''kakos'' "bad") was the term used by Jeremy Bentham in his 1818 Plan of Parliamentary Reform (Works, vol. 3, p. 493). ...
n surveillance state.
Here are a few other works that focus on mass surveillance:
* '' We'', a 1920 novel by Russian author Yevgeny Zamyatin
Yevgeny Ivanovich Zamyatin ( rus, Евге́ний Ива́нович Замя́тин, p=jɪvˈɡʲenʲɪj ɪˈvanəvʲɪtɕ zɐˈmʲætʲɪn; – 10 March 1937), sometimes anglicized as Eugene Zamyatin, was a Russian author of science fictio ...
, that predates ''Nineteen Eighty-Four
''Nineteen Eighty-Four'' (also stylised as ''1984'') is a dystopian social science fiction novel and cautionary tale written by the English writer George Orwell. It was published on 8 June 1949 by Secker & Warburg as Orwell's ninth and fina ...
'' and was read by its author George Orwell.
* '' Little Brother'' is a novel by Cory Doctorow
Cory Efram Doctorow (; born July 17, 1971) is a Canadian-British blogger, journalist, and science fiction author who served as co-editor of the blog ''Boing Boing''. He is an activist in favour of liberalising copyright laws and a proponent of ...
, and is set in San Francisco after a major terrorist attack. The DHS uses technologies such as RFIDs and surveillance cameras to create a totalitarian system of control.
* ''The Lives of Others
''The Lives of Others'' (german: link=no, Das Leben der Anderen, ) is a 2006 German drama film written and directed by Florian Henckel von Donnersmarck marking his feature film directorial debut. The plot is about the monitoring of East Berl ...
'', is a 2006 German drama film, which conveys the impact that relentless surveillance has on the emotional well-being and the outcome of individuals subjected to it.
* ''The Hunger Games
''The Hunger Games'' is a series of young adult dystopian novels written by American author Suzanne Collins. The first three novels are part of a trilogy following teenage protagonist Katniss Everdeen, and the fourth book is a prequel set 6 ...
'' by Suzanne Collins
Suzanne Collins (born August 10, 1962) is an American author and television writer. She is known as the author of the book series '' The Underland Chronicles'' and ''The Hunger Games''.
Early life
Suzanne Collins was born on August 10, 1962, i ...
is a trilogy in which 'the Capitol' has totalitarian surveillance and control over all aspects of the other 'districts'.
* ''Digital Fortress
''Digital Fortress'' is a techno-thriller novel written by American author Dan Brown and published in 1998 by St. Martin's Press. The book explores the theme of government surveillance of electronically stored information on the private lives of ...
'', novel by Dan Brown
Daniel Gerhard Brown (born June 22, 1964) is an American author best known for his thriller novels, including the Robert Langdon novels ''Angels & Demons'' (2000), '' The Da Vinci Code'' (2003), ''The Lost Symbol'' (2009), '' Inferno'' (2013), ...
, involving an NSA code breaking machine called 'TRANSLTR'. The machine read and decrypted email messages, with which the NSA used to foil terrorist attacks and mass murders.
* Valve's 2004 video game ''Half-Life 2
''Half-Life 2'' is a 2004 first-person shooter game developed by Valve Corporation, Valve. It was published by Valve through its distribution service Steam (service), Steam. Like the original ''Half-Life (video game), Half-Life'' (1998), ''Half- ...
'' is set in City 17, a fictional police state in Eastern Europe
Eastern Europe is a subregion of the Europe, European continent. As a largely ambiguous term, it has a wide range of geopolitical, geographical, ethnic, cultural, and socio-economic connotations. The vast majority of the region is covered by Russ ...
in which citizens are under constant surveillance.
* The Ubisoft
Ubisoft Entertainment SA (; ; formerly Ubi Soft Entertainment SA) is a French video game publisher headquartered in Saint-Mandé with development studios across the world. Its video game franchises include '' Assassin's Creed'', ''Far Cry'', '' ...
video game series ''Watch Dogs
''Watch Dogs'' (stylized as ''WATCH_DOGS'') is an action-adventure video game franchise published by Ubisoft, and developed primarily by its Montreal and Toronto studios using the Disrupt game engine. The series' eponymous first title was rel ...
'' is set in the near future with AI connected cities that use surveillance systems to monitor their people in increasingly invasive ways. In particular, '' Watch Dogs: Legion'' is set in a dystopian London
London is the capital and largest city of England and the United Kingdom, with a population of just under 9 million. It stands on the River Thames in south-east England at the head of a estuary down to the North Sea, and has been a majo ...
where an oppressive regime has taken power and incorporates heavy use of surveillance software to control the populace following a series of terrorist attacks.
See also
* 2013 global surveillance disclosures *Broken windows theory
In criminology, the broken windows theory states that visible signs of crime, anti-social behavior and civil disorder create an urban environment that encourages further crime and disorder, including serious crimes. The theory suggests that po ...
, a controversial theory that maintaining and monitoring urban environments in a well-ordered condition may stop further vandalism and escalation into more serious crime.
* Cellphone surveillance
* Closed-circuit television
Closed-circuit television (CCTV), also known as video surveillance, is the use of video cameras to transmit a signal to a specific place, on a limited set of monitors. It differs from broadcast television in that the signal is not openly t ...
(CCTV)
* Computer and network surveillance
Computer and network surveillance is the monitoring of computer activity and data stored locally on a computer or data being transferred over computer networks such as the Internet. This monitoring is often carried out covertly and may be comple ...
* COVID-19 surveillance
COVID-19 surveillance involves monitoring the spread of the coronavirus disease in order to establish the patterns of disease progression. The World Health Organization (WHO) recommends active surveillance, with focus of case finding, testing a ...
* Data privacy
Information privacy is the relationship between the collection and dissemination of data, technology, the public expectation of privacy, contextual information norms, and the legal and political issues surrounding them. It is also known as data pr ...
* Data retention Data retention defines the policies of persistent data and records management for meeting legal and business data archival requirements. Although sometimes interchangeable, it is not to be confused with the Data Protection Act 1998.
The different ...
* '' Discipline and Punish: The Birth of the Prison'', a 1975 book by the French philosopher Michel Foucault
Paul-Michel Foucault (, ; ; 15 October 192625 June 1984) was a French philosopher, historian of ideas, writer, political activist, and literary critic. Foucault's theories primarily address the relationship between power and knowledge, and how ...
.
*
* Global surveillance
Global mass surveillance can be defined as the mass surveillance of entire populations across national borders.
Its existence was not widely acknowledged by governments and the mainstream media until the global surveillance disclosures by Edwar ...
* Government databases A government database collects information for various reasons, including climate monitoring, securities law compliance, geological surveys, patent applications and grants, surveillance, national security, border control, law enforcement, public hea ...
* IT-backed authoritarianism
IT-backed authoritarianism, also known as techno-authoritarianism, digital authoritarianism or digital dictatorship, refers to the state use of information technology in order to control or manipulate both foreign and domestic populations. Tactic ...
* Lawful interception Lawful interception (LI) refers to the facilities in telecommunications and telephone networks that allow law enforcement agencies with court orders or other legal authorization to selectively wiretap individual subscribers. Most countries require ...
* List of government surveillance projects
This is a list of government surveillance projects and related databases throughout the world.
International
* ECHELON: A signals intelligence (SIGINT) collection and analysis network operated on behalf of the five signatory states to the ...
* National security
National security, or national defence, is the security and defence of a sovereign state, including its citizens, economy, and institutions, which is regarded as a duty of government. Originally conceived as protection against military atta ...
* Network analysis Network analysis can refer to:
* Network theory, the analysis of relations through mathematical graphs
** Social network analysis, network theory applied to social relations
* Network analysis (electrical circuits)
See also
*Network planning and ...
* Nothing to hide argument
The nothing to hide argument states that individuals have no reason to fear or oppose surveillance programs, unless they are afraid it will uncover their own illicit activities. An individual using this argument may claim that an average person s ...
* Pen register
A pen register, or dialed number recorder (DNR), is an electronic device that records all numbers called from a particular telephone line. The term has come to include any device or program that performs similar functions to an original pen regi ...
, originally an electronic device that records numbers (but not the audio) called from a particular telephone line, more recently any device or program that performs this function for electronic mail, other digital communications, and particularly communications over the Internet.
* Phone surveillance
* Police state
A police state describes a state where its government institutions exercise an extreme level of control over civil society and liberties. There is typically little or no distinction between the law and the exercise of political power by the ...
* Radio-frequency identification (RFID), the wireless identification and tracking of tags attached to objects.
* Right to privacy
The right to privacy is an element of various legal traditions that intends to restrain governmental and private actions that threaten the privacy of individuals. Over 150 national constitutions mention the right to privacy. On 10 December 194 ...
* Security culture
Security culture is a set of practices used by activists, notably contemporary anarchists, to avoid, or mitigate the effects of, police surveillance and harassment and state control.
Overview
Security culture recognizes the possibility that ana ...
* Signals intelligence
Signals intelligence (SIGINT) is intelligence-gathering by interception of ''signals'', whether communications between people (communications intelligence—abbreviated to COMINT) or from electronic signals not directly used in communication ( ...
(SIGINT)
* Sousveillance
Sousveillance ( ) is the recording of an activity by a member of the public, rather than a person or organisation in authority, typically by way of small wearable or portable personal technologies. The term, coined by Steve Mann, stems from th ...
, the recording of an activity by a participant in the activity, cameras (or other sensors) affixed to property, or surveillance done by non-authorities.
* Stakeholder theory
* Surveillance capitalism
Surveillance capitalism is a concept in political economics which denotes the widespread collection and commodification of personal data by corporations. This phenomenon is distinct from government surveillance, though the two can reinforce each o ...
* Telephone tapping in the Eastern Bloc
Telephone tapping in the Eastern Bloc was a widespread method of the mass surveillance of the population by the secret police.
History
In the past, telephone tapping was an open and legal practice in certain countries. During martial law in Polan ...
* Tracking system
A tracking system, also known as a locating system, is used for the observing of persons or objects on the move and supplying a timely ordered sequence of location data for further processing. It is important to be aware of human tracking, fu ...
* Traffic analysis
Traffic analysis is the process of intercepting and examining messages in order to deduce information from patterns in communication, it can be performed even when the messages are encrypted. In general, the greater the number of messages observed ...
References
External links
*"The State and Surveillance: Fear and Control"
Didier Bigo and Mireille Delmas-Marty, ''La Clé des Langues'', 23 September 2011,. {{DEFAULTSORT:Mass Surveillance * Human rights Security National security Law enforcement Law enforcement techniques Crime prevention Counterterrorism